Corporate cybersecurity awareness training in a modern office
Security Awareness Best Practices Guide
Let's talk numbers. A single cybersecurity breach in 2026 cost companies $4.88 million on average. That's not the worst part, though. People—your colleagues, employees, maybe even you—accidentally triggered 82% of these attacks.
Your company might run enterprise-grade firewalls. You've probably got encryption that would make cryptographers weep with joy. But here's the thing: none of that technical wizardry matters when Karen from accounting clicks a sketchy link, or when Dave uses "Winter2025!" for literally everything from Salesforce to the corporate VPN.
Organizations that actually commit to proper training see phishing attacks drop by 70%. They handle incidents 52% faster. Your cyber insurance premiums? They'll decrease when you document real training efforts. And those dreaded compliance audits become far less nightmarish.
Want a cautionary tale? Mid-sized healthcare provider, about 300 employees. Someone clicked what appeared to be a legitimate vendor invoice. Ransomware locked everything. Six days offline. Recovery costs hit $2.3 million, plus HIPAA violation fines on top. They could've run a comprehensive awareness program for five years straight with that money—annual cost would've been around $45,000.
Do the math yourself. Five hundred employees, $75 each yearly for solid training. That's $37,500 total. One prevented breach pays for the program multiple times over. Plus there's something you can't quantify: turning your workforce into active defenders instead of accidental saboteurs.
Core Components of Effective Security Awareness Programs
Four things make or break your security awareness efforts: clear policies everyone understands, training that doesn't bore people to tears, measurement that actually matters, and constant refinement based on what you learn.
Start with policies. You need acceptable use guidelines, password rules, data handling procedures, incident reporting processes. But—and this matters tremendously—write these in language real humans speak. Skip the legal jargon. A manufacturing company had this 47-page security manual. Guess how many people read it? Nearly zero. They condensed everything into 12 pages with actual visual examples. Policy violations dropped 63% within six months.
The most sophisticated security infrastructure crumbles when an employee reuses passwords or falls for social engineering. We've seen organizations spend millions on tools while neglecting the $50,000 investment in training that would have actually stopped the breach
— Sarah Chen
Training delivery needs to match how brains work. Those hour-long sessions where everyone multitasks and checks email? Useless. Five-minute modules people can knock out during coffee breaks? Much better. Interactive simulations where choices have consequences? Even better. And you've got to reinforce quarterly because people forget—it's biology, not laziness.
Measurement systems separate fantasy from reality. Sure, track who completed training. But completion rates mean nothing if nobody learned anything. Run phishing simulations. Analyze incident reports. Check help desk tickets. Those metrics tell you what's actually happening.
Continuous improvement means reviewing everything quarterly and adapting. Financial services firm discovered through testing that 40% of employees couldn't identify business email compromise attempts. They built targeted modules addressing exactly that weakness. Within two months, susceptibility dropped 55%.
Building a Security-First Culture
Culture shifts happen when security becomes second nature, not some annual requirement people resent. You need leadership that demonstrates what matters, positive reinforcement instead of threats, and systems designed so secure choices require less effort than risky ones.
Leadership sets the tone. When your CEO discusses security concerns openly, completes the same training everyone else does, and admits their own close calls with phishing attempts—that normalizes security awareness faster than any mandatory policy ever could. Tech company CEO shared publicly how he almost fell for a sophisticated phishing email. That single story created more cultural impact than dozens of training modules combined.
Try gamification. Security champion programs, friendly competitions between departments, recognition for spotting and reporting threats. When employees view security as everyone's mission instead of just IT's headache, your program scales exponentially. Retail chain launched store-level security champions—point-of-sale compromise attempts fell 71%.

Author: Alyssa Norwood;
Source: elegantimagerytv.com
Engaging Stakeholders and Leadership
Getting executives on board? Speak their language. They care about business risk, not technical architecture. Frame everything around protecting revenue, safeguarding reputation, maintaining competitive advantage. Board presentations should focus on breach costs, regulatory exposure, insurance implications—not training platform features.
Department managers need context for their specific teams. Show marketing why their customer database access creates unique responsibilities. Help HR understand why their systems attract social engineering attacks. Make finance understand wire transfer fraud tactics. Generic messaging that applies to everyone resonates with no one.
Budget approval requires demonstrable outcomes. Track reduced incident response costs, fewer help desk tickets for compromised accounts, improved audit scores. Logistics company documented $180,000 in prevented fraud attempts that trained employees identified and reported. That justified tripling their program budget.
How Security Awareness Best Practices Work in Real Environments
Begin with baseline assessment. Send unannounced phishing simulations—see who clicks. Survey employees about security knowledge. Review past incidents for failure patterns. This data reveals where to focus initial efforts rather than guessing.
Phased rollout prevents overwhelming people. First month tackles password hygiene and multi-factor authentication. Second month introduces phishing recognition. Third month covers physical security and clean desk policies. Staggering topics ensures each receives proper attention before moving forward.
Integration matters. Connect with your learning management system so security training sits alongside other professional development. Set up single sign-on to reduce friction. Use calendar invitations during natural breaks—don't interrupt critical deadline work.
Behavioral change follows a predictable arc: awareness, understanding, practice, habit. Initial training creates threat awareness. Simulations and concrete examples build recognition skills. Regular testing provides practice. Consistent reinforcement over 6-12 months creates automatic habits that don't require constant conscious thought.
Manufacturing company rolled this out systematically. Started with a 15-minute overview video. Two weeks later, they sent a fake phishing email—78% of employees clicked it. Ouch. After targeted training for clickers plus monthly simulations, click rates dropped to 12% within six months. By month twelve, employees were proactively forwarding 15-20 suspicious emails weekly to IT for analysis.
Author: Alyssa Norwood;
Source: elegantimagerytv.com
Security Awareness Best Practices Examples by Threat Type
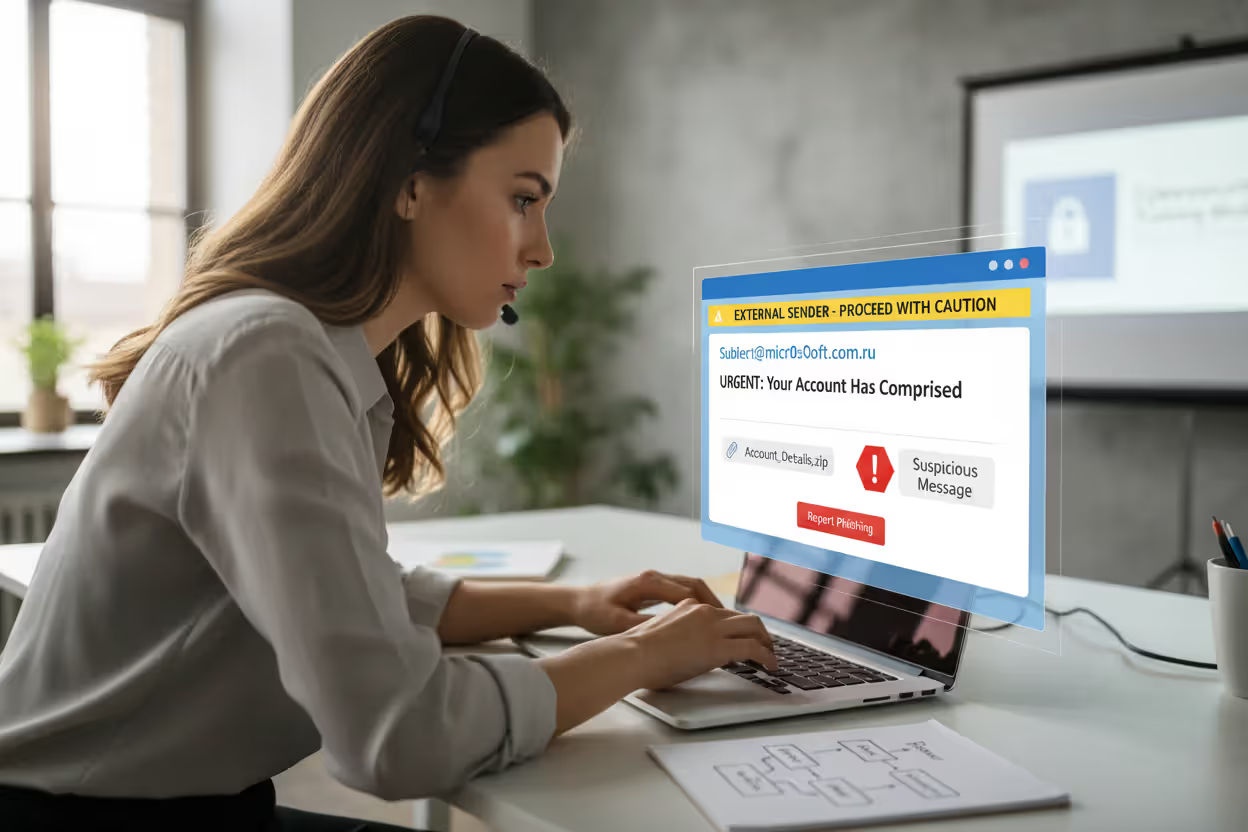
Phishing and Email Security
Teach the hover technique—mouse over sender names to reveal actual email addresses underneath display names. Point out urgency language ("Wire this NOW!"), suspicious attachments, requests to bypass normal procedures. Install one-click reporting buttons directly in email clients.
University implemented their "STOP" method: Sender verification, Tone assessment (urgency or fear tactics), Offers seeming too good to be true, Personal information requests. They reinforced with monthly simulated attacks that gradually increased in sophistication. Successful phishing attempts dropped 84%.
Password Hygiene
Ditch "use complex passwords"—teach passphrase creation. "Coffee-Morning-Sunshine-42" beats "C0ff33!" in both memorability and security. Emphasize unique passwords per system, not slight variations on one theme. Explain credential stuffing attacks that exploit password reuse.
Actually deploy password managers, then train people to use them. Employees who understand how managers work adopt them 89% more consistently. Consulting firm reduced password-related help desk tickets 67% within three months after deploying enterprise password management with proper onboarding.
Social Engineering Defense
Role-play the scenarios people actually face. The fake IT support call requesting credentials. The "CEO" demanding urgent wire transfers. The vendor updating payment information. Practice verification procedures—call known numbers, don't use contact info provided in suspicious requests.
Hammer home this point: legitimate requests can wait for verification. Hospital prevented a $340,000 wire fraud when an accounts payable clerk remembered training about verifying unusual payment requests through separate communication channels before proceeding.
Mobile Security
Address personal device risks in bring-your-own-device environments, because that's reality now. Teach recognition of malicious apps. Explain why public Wi-Fi without VPN protection exposes work tasks. Demonstrate enabling remote wipe. Actually show people how easily attackers intercept unencrypted traffic at Starbucks.
Sales organization reduced mobile-related incidents 73% after implementing quarterly mobile security refreshers that included hands-on VPN connection practice and identifying suspicious app permissions.

Author: Alyssa Norwood;
Source: elegantimagerytv.com
Remote Work Scenarios
Cover home network basics. Video call privacy—seriously, don't discuss mergers in public coffee shops. Secure file sharing versus emailing attachments. Address the blurred lines between personal and professional device use that everyone navigates now. Teach secure disposal of printed materials and screen positioning that prevents shoulder surfing by family members or that Instacart delivery person.
Remote work's rapid expansion exposed vulnerabilities nobody anticipated. Organizations addressing home office security specifically saw 58% fewer incidents compared to those applying generic office-based training to remote contexts without adaptation.
Common Mistakes That Undermine Security Awareness Efforts
Annual-Only Training
Security awareness fades faster than you'd think. Employees retain maybe 40% after one month. Only 20% sticks past six months without review. Annual training creates compliance checkmarks but changes zero behaviors. Monthly bite-sized content or quarterly refreshers maintain functional awareness levels.
Financial institution switched from annual sessions to monthly 5-minute modules. Retention scores jumped from 31% to 76% when tested six months post-training.
Ignoring Metrics
Programs without measurement operate blindfolded. Completion rates reveal nothing—people click through while learning absolutely nothing. Phishing simulation results, actual incident rates, behavioral observations provide actionable intelligence. Organizations actively tracking and responding to metrics achieve 3.2 times better outcomes than those watching completion percentages alone.
One-Size-Fits-All Content
Generic training connects with nobody. Developers face different threats than customer service reps. Executive assistants need specific business email compromise training. Warehouse staff require physical security emphasis. Role-tailored content increases relevance and retention 67% compared to generic modules everyone ignores.
Lack of Executive Buy-In
When leadership treats security awareness as IT's problem, employees follow that example immediately. Programs succeed when executives participate visibly, discuss security in company communications, allocate meaningful resources. Retail chain's program languished at 23% engagement until their CEO included monthly security tips in company newsletters—engagement jumped to 81% within four months.
Compliance-Only Mindset
Treating training as regulatory checkbox theater produces minimal results. Employees sense instantly when organizations care only about avoiding fines rather than actual protection. Compliance-focused programs achieve 42% lower behavioral change rates than those genuinely invested in building security culture.
Measuring and Improving Your Security Awareness Program
Effective measurement combines hard data with qualitative assessment. Track these indicators quarterly:

Author: Alyssa Norwood;
Source: elegantimagerytv.com
Phishing Simulation Results: What percentage click malicious links, enter credentials, open dangerous attachments? Below 10% signals program maturity. Focus on trends over time rather than obsessing over individual test results.
Incident Rates: Monitor security incidents caused by human error specifically. Decreasing trends validate program effectiveness. Break down by incident type to identify stubborn weak areas needing additional focus.
Reporting Rates: Count employee-initiated reports of suspicious emails, calls, activities. Increasing reports indicate growing awareness and engagement. Healthy programs generate 10-15 reports per 100 employees monthly, even when most turn out to be false alarms—that's fine.
Training Completion and Knowledge Retention: Track who completed training, yes, but also assessment scores showing actual comprehension. Scores below 80% suggest content complexity issues or poor explanations.
Time to Detect and Report: Measure how quickly employees identify and report threats. Mature programs achieve average reporting within 15 minutes of receiving suspicious emails.
| Training Approach | Success Rate | Ideal Application | Complexity | Annual Investment |
| Hands-On Simulations | Very High (85-92%) | Decision-making practice | Moderate setup | $75-150 per person |
| Brief Learning Modules | High (78-85%) | Ongoing reinforcement | Easy deployment | $30-60 per person |
| Fake Phishing Tests | High (80-88%) | Email security assessment | Simple launch | $25-50 per person |
| Live Workshop Sessions | Moderate (65-75%) | Program kickoff | Significant effort | $150-300 per person |
| Video-Based Learning | Moderate (60-70%) | Policy introduction | Minimal work | $20-40 per person |
| Game-Style Platforms | High (75-83%) | Sustained engagement | Moderate configuration | $50-100 per person |
Testing methods should vary constantly to avoid predictability. Rotate phishing simulation themes, timing, complexity levels. Include SMS-based attacks, voice calls (vishing), physical security tests like tailgating attempts. Employees who learn tests arrive every first Tuesday will only stay alert on first Tuesdays.
Feedback loops close gaps between testing and learning. When someone fails a simulation, provide immediate constructive guidance instead of punishment. "You clicked a simulated phishing link—here's what to watch for next time" works infinitely better than "You failed the security test."
Benchmarking against industry standards provides helpful context. Healthcare organizations average 18% phishing click rates. Financial services average 12%. Understanding where your organization stands helps establish realistic improvement targets.
Adapting to emerging threats requires monitoring the landscape continuously and updating content fast. When deepfake voice attacks emerged as significant threats in 2025, leading programs added voice verification training within weeks. Quarterly threat briefings from your security team should directly inform training content updates.
Technology company's measurement approach demonstrates comprehensive tracking. They monitor phishing click rates (currently 8%), monthly security reports per employee (0.14), average incident response time (12 minutes), training completion within deadline (94%), post-training assessment scores (87% average). Quarterly reviews guide content adjustments based on weak areas. They've documented $420,000 in prevented losses over two years.
Frequently Asked Questions About Security Awareness Best Practices
Effective security awareness transforms employees from biggest vulnerability into strongest defense. Organizations investing in comprehensive, ongoing training see measurable attack reductions, faster incident response, stronger security cultures overall. The foundation requires clear policies, engaging delivery, consistent measurement, continuous improvement responding to emerging threats.
Success depends on moving beyond annual compliance theater toward integrated security awareness woven into daily operations. When executives model secure behaviors, employees receive role-specific training, and organizations actively measure and respond to program metrics, behavioral change follows naturally.
Investment in robust security awareness programs—typically $30-150 per employee annually—looks trivial compared to breach expenses averaging $4.88 million. Well-trained employees who recognize and report threats prevent countless incidents that never appear in cost calculations but would've caused devastating damage.
Start by assessing current vulnerabilities establishing where you stand today. Implement staggered rollout focused on highest-risk areas first. Establish measurement systems tracking progress objectively. Adjust content quarterly based on testing results and emerging threat patterns. With consistent effort over 6-12 months, you'll create a security-first culture where awareness becomes automatic habit rather than forced obligation.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to cybersecurity awareness, online threats, phishing attacks, and data protection practices.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity risks and protection strategies may vary depending on individual behavior, technology usage, and threat environments.
This website does not provide professional cybersecurity, legal, or technical advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.