Complete Guide to Cybersecurity Awareness

Author: James Smith;
Source: elegantimagerytv.com
Welcome to the Cybersecurity Awareness Knowledge Hub, a place where individuals, employees, and small businesses can learn how to recognize and respond to modern cyber threats. Cybersecurity awareness is an essential part of staying safe online, helping people understand how cyberattacks happen and how sensitive information can be protected.
This website focuses on explaining cybersecurity in a clear and practical way. Many users encounter unfamiliar concepts when learning about phishing, scams, malware, ransomware, and authentication methods. The goal of this resource is to make these topics easier to understand by providing straightforward explanations of how cyber threats work and how they can be prevented.
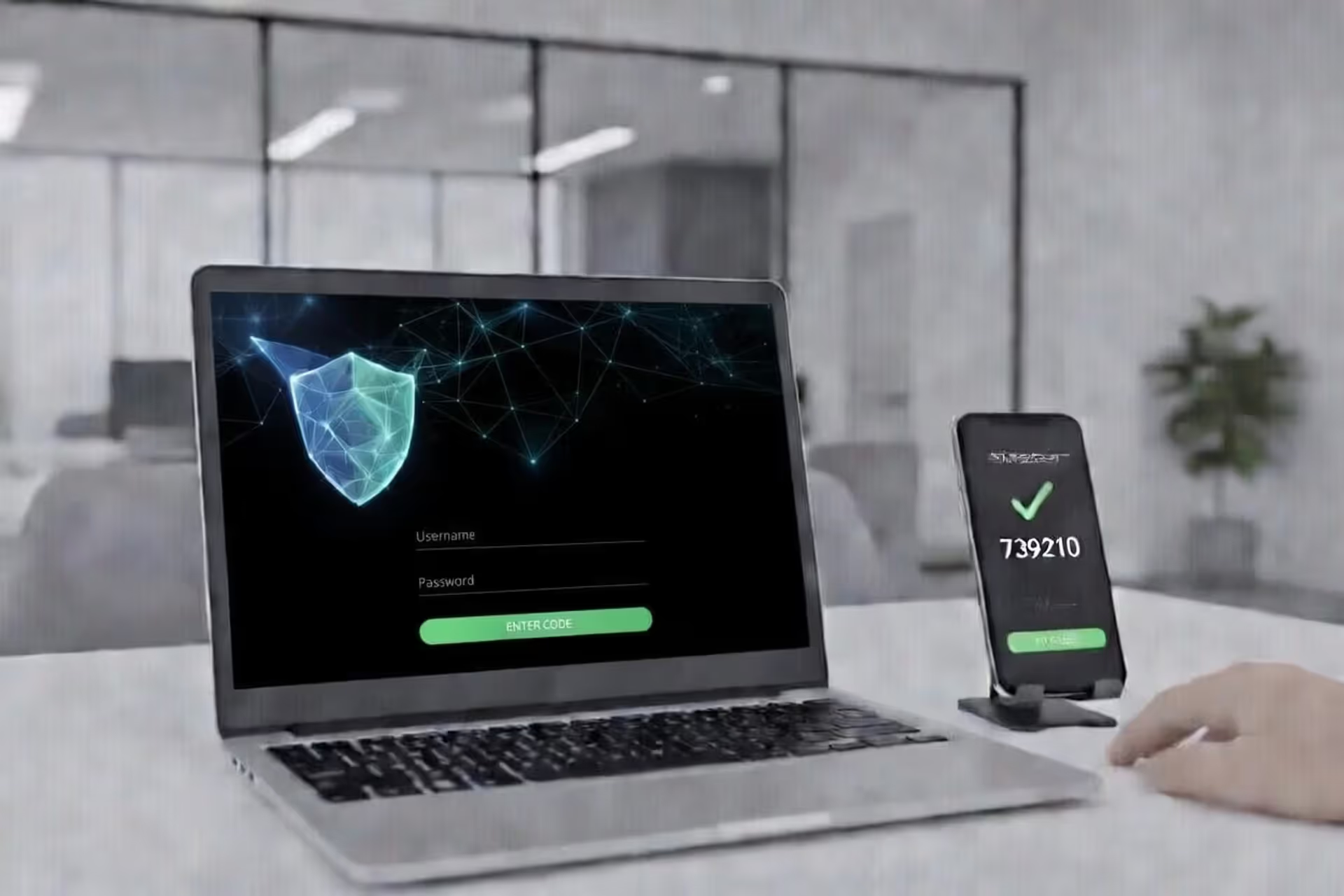
Throughout the site, readers can explore topics related to phishing attacks, online scams, password security, and multi-factor authentication (MFA). The content also discusses common threats such as malware, ransomware, and brute force attacks, as well as best practices for cyber hygiene and risk management. In addition, the site explains how cybersecurity awareness connects with everyday online activities, including email use, browsing, and protecting personal and business data.
Read more

Top Stories

Read more

Read more

Read more
Read more
Trending
Read more

Read more
Latest articles













Most read

Read more

Read more
In depth
Found out a scammer grabbed your email address? Here's what that actually means for you. Your email isn't just another account—it's the master key to your digital life. Banking apps, social networks, Amazon orders, medical portals, work systems—they all tie back to that one address.
When criminals get hold of it, they haven't broken into your house yet. But they're standing on your porch, trying different keys. The question isn't whether they'll attempt something. It's how fast you can lock them out before they succeed.
Here's the thing most people miss: there's a massive difference between someone knowing your email address and someone controlling your email account. One's a threat. The other's a crisis. Figuring out which situation you're facing shapes everything you do next.
How Scammers Use Your Email Address
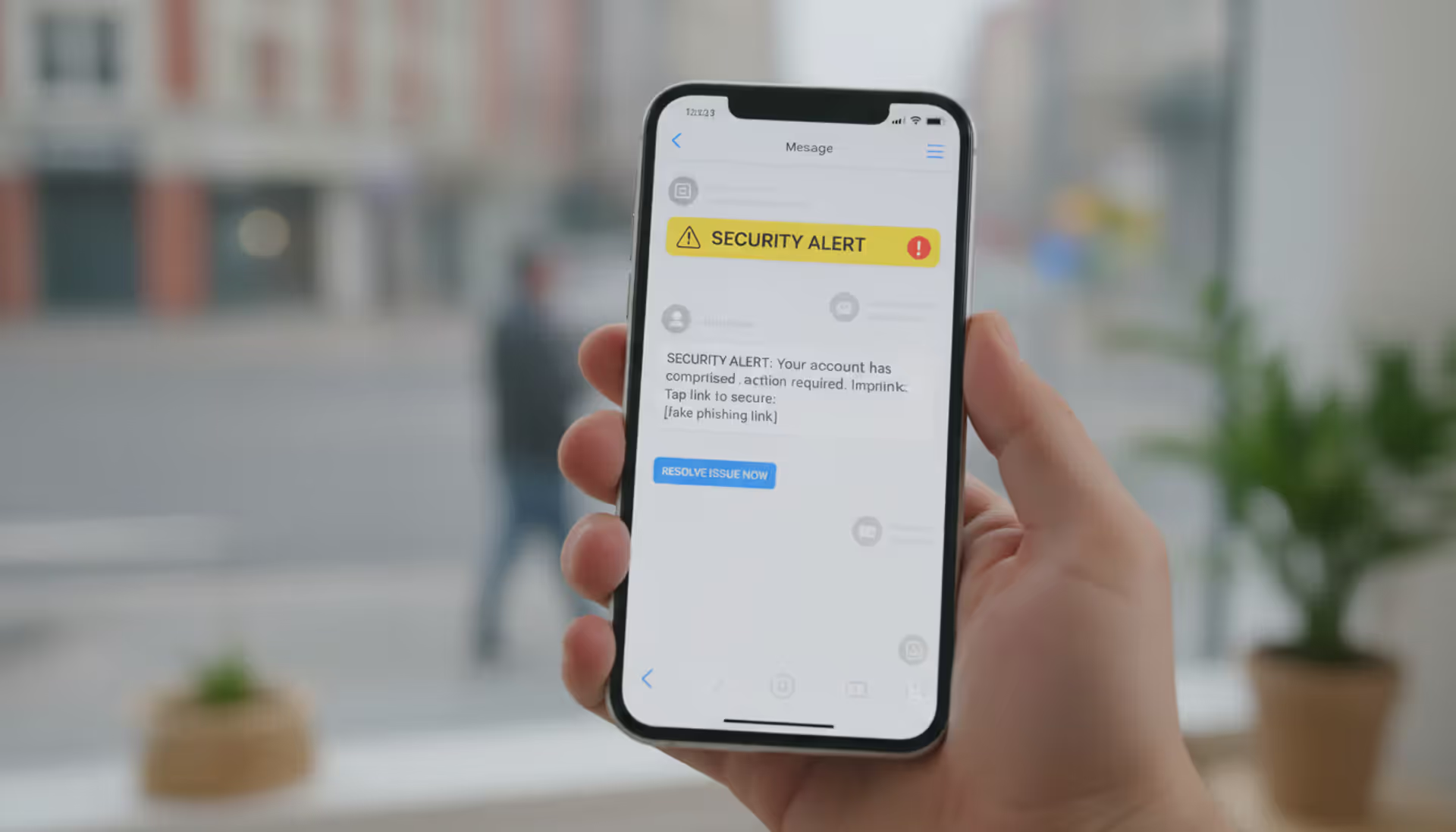
Criminals don't just send spam when they get your email. They deploy it across multiple attack strategies, each escalating in severity.
Phishing campaigns top the list. Fraudsters craft messages that mimic your bank, favorite retailers, or government offices. These messages push you toward counterfeit websites—carbon copies of real login screens—where anything you type flows directly to the scammers. The FTC logged phishing as the source of 36% of fraud reports in 2025, with victims losing an average of $1,200 each.
Account takeover attempts follow a formula. Criminals fire off password reset requests to Netflix, Amazon, PayPal, and dozens of other services. They're gambli...
Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to cybersecurity awareness, online threats, phishing attacks, and data protection practices.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity risks and protection strategies may vary depending on individual behavior, technology usage, and threat environments.
This website does not provide professional cybersecurity, legal, or technical advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.





