Cybersecurity concept with digital protection interfaces and secure network environment
What Does Cyber Security Do?
Digital threats evolve faster than most organizations can adapt. Every 39 seconds, a cyberattack occurs somewhere in the world, targeting businesses, governments, and individuals alike. Cybersecurity stands as the primary defense mechanism against these relentless threats, protecting everything from financial records to intellectual property.
The discipline encompasses far more than installing antivirus software or creating strong passwords. It represents a comprehensive approach to safeguarding digital assets through layered defenses, continuous monitoring, and rapid response protocols. Understanding what cybersecurity actually does helps organizations allocate resources effectively and individuals protect their personal information from increasingly sophisticated attacks.
How Cyber Security Protects Organizations and Individuals
The purpose of cyber security extends beyond simply blocking threats at the perimeter. Modern protection operates through multiple interconnected layers that work simultaneously to detect, prevent, and respond to malicious activity.
Threat detection systems continuously scan network traffic, user behavior, and system logs for anomalies that signal potential attacks. These systems use baseline patterns established during normal operations to identify deviations—a login attempt from an unusual geographic location, file access patterns that don't match typical user behavior, or network traffic spikes that suggest data exfiltration.
Prevention mechanisms create barriers before threats reach critical systems. Access controls ensure users only reach resources necessary for their roles. Patch management systems automatically update software vulnerabilities that attackers commonly exploit. Email filtering stops phishing attempts before employees encounter them. These preventive measures reduce the attack surface available to malicious actors.
Monitoring systems provide 24/7 visibility across the entire digital infrastructure. Security Operations Centers (SOCs) track thousands of events per second, correlating data from firewalls, endpoints, cloud services, and applications. This constant vigilance catches threats that slip past initial defenses, often within minutes rather than the months-long dwell times seen in organizations without robust monitoring.

Author: Trevor Kingsland;
Source: elegantimagerytv.com
Real-time response capabilities activate immediately when threats are confirmed. Automated systems can isolate compromised devices, block malicious IP addresses, and terminate suspicious processes without waiting for human intervention. This speed matters tremendously—ransomware can encrypt thousands of files in under an hour, making rapid response the difference between a minor incident and a catastrophic breach.
How cyber security works in practice involves coordination between these elements. A phishing email might pass through email filters but get flagged when the recipient clicks a malicious link. Endpoint protection blocks the malware download. If the malware somehow executes, behavior monitoring detects its encryption attempts and isolates the device before significant damage occurs. This defense-in-depth approach ensures that no single point of failure compromises the entire system.
Cybersecurity has transitioned from a technical checkbox to a business imperative. Organizations that view it merely as IT overhead rather than strategic protection consistently face the highest breach costs and longest recovery times
— Vice President of Cloud Security and CISO Advisor at Rubrik
Core Responsibilities of Cyber Security Professionals
The role of cyber security professionals encompasses diverse tasks that shift based on immediate threats and long-term strategic goals. Daily activities rarely follow a predictable routine, particularly in environments facing active threats.
Security analysts spend significant time reviewing alerts generated by monitoring systems. Not every alert indicates a genuine threat—false positives outnumber real incidents by substantial margins in many environments. Analysts must quickly distinguish between benign anomalies and actual attacks, investigating suspicious activity through log analysis, network traffic examination, and endpoint forensics.
Incident response becomes the priority when breaches occur. Professionals must contain the threat, eradicate malicious presence, and restore normal operations while preserving evidence for potential legal proceedings. A financial services firm facing a ransomware attack might need to decide within hours whether to pay the ransom, restore from backups, or rebuild systems from scratch—each option carrying significant implications for business continuity and regulatory compliance.
Vulnerability assessments identify weaknesses before attackers exploit them. Security teams regularly scan networks, applications, and systems for known vulnerabilities, then prioritize remediation based on risk levels. A critical vulnerability in a public-facing web application receives immediate attention, while a low-severity issue in an isolated internal system might wait for the next maintenance window.
Security audits verify that policies and controls actually function as intended. Professionals review access logs to ensure terminated employees no longer have system access, confirm that encryption protects sensitive data at rest and in transit, and validate that backup systems can actually restore data during disasters. These audits often reveal gaps between documented policies and actual implementation.
Policy enforcement ensures that security standards apply consistently across the organization. This cyber security responsibility includes educating employees about security practices, reviewing requests for security exceptions, and working with other departments to implement controls without unnecessarily hindering business operations. The challenge lies in maintaining security while enabling productivity—overly restrictive policies drive users toward dangerous workarounds.
Key Functions Cyber Security Performs Across Industries
Different cyber security functions address specific aspects of digital protection, each critical to comprehensive defense strategies. Organizations typically implement multiple functions simultaneously, creating overlapping protection layers.
| Cyber Security Function | What It Protects | Common Tools Used | Industries That Rely On It |
| Network Security | Data in transit, internal communications, remote access | Firewalls, VPNs, IDS/IPS, network segmentation | Healthcare, finance, manufacturing, government |
| Application Security | Software vulnerabilities, API endpoints, user inputs | WAF, SAST/DAST tools, secure coding frameworks | E-commerce, SaaS providers, fintech, gaming |
| Cloud Security | Virtual infrastructure, containerized apps, cloud storage | CASB, CSPM, cloud-native security tools | Tech companies, startups, enterprises with hybrid infrastructure |
| Identity Management | User credentials, access privileges, authentication | IAM platforms, MFA, SSO, PAM | All industries, particularly those with remote workforces |
| Data Security | Sensitive information, intellectual property, customer data | Encryption, DLP, tokenization, data masking | Healthcare, legal, financial services, retail |
| Endpoint Security | Laptops, mobile devices, IoT devices, servers | EDR, antivirus, mobile device management | All industries with distributed workforces or IoT deployments |
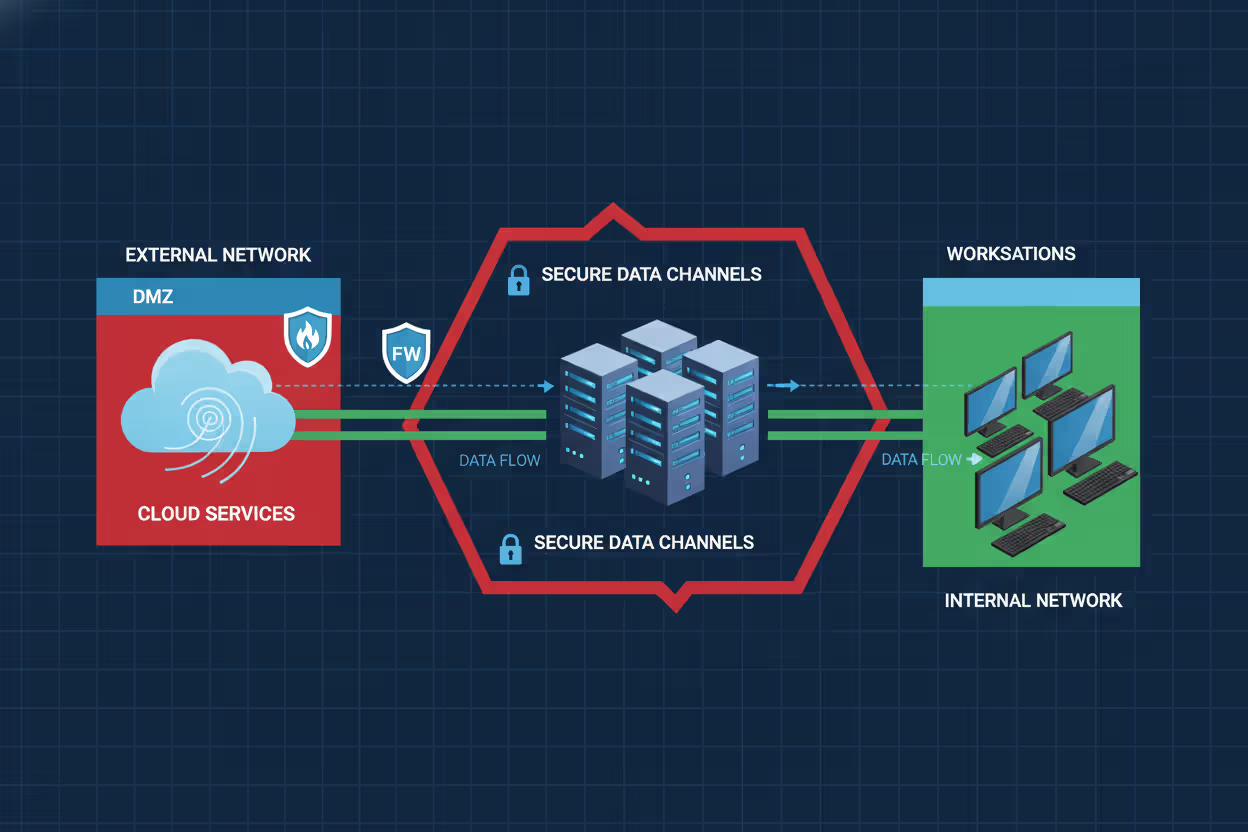
Network Security and Infrastructure Protection
Network security establishes the foundation for all other security measures by controlling how data moves between systems. Firewalls act as gatekeepers, permitting legitimate traffic while blocking suspicious connections based on predefined rules. Modern next-generation firewalls inspect traffic at the application layer, identifying threats hidden within seemingly normal communications.
Network segmentation divides infrastructure into isolated zones, preventing attackers who breach one area from freely moving throughout the environment. A retail company might separate point-of-sale systems from corporate networks, ensuring that a compromised cash register can't provide access to customer databases or financial systems.
Virtual Private Networks (VPNs) create encrypted tunnels for remote workers, protecting data as it travels across public internet connections. However, VPNs introduce their own risks—a compromised remote device with VPN access can serve as an entry point for attackers, which is why many organizations now implement zero-trust architectures that verify every access request regardless of network location.
Author: Trevor Kingsland;
Source: elegantimagerytv.com
Data Encryption and Privacy Management
Encryption transforms readable data into scrambled formats that remain useless without the correct decryption keys. This cyber security function protects information even when other defenses fail—stolen encrypted data provides no value to attackers who lack the keys.
Organizations encrypt data at rest (stored on servers or devices) and data in transit (moving across networks). Healthcare providers encrypt patient records to comply with HIPAA requirements. Financial institutions encrypt transaction data to prevent fraud. Cloud storage services encrypt files to protect against unauthorized access by their own employees.
Privacy management extends beyond encryption to include data minimization (collecting only necessary information), access controls (limiting who can view sensitive data), and retention policies (deleting data when no longer needed). California's CCPA and other privacy regulations make these practices legal requirements rather than optional safeguards.

Author: Trevor Kingsland;
Source: elegantimagerytv.com
Threat Intelligence and Risk Assessment
Threat intelligence gathering provides early warning about emerging attack methods, vulnerable software, and threat actor tactics. Security teams subscribe to intelligence feeds that share information about newly discovered vulnerabilities, active malware campaigns, and compromised credentials circulating on dark web markets.
Risk assessments evaluate which assets face the greatest threats and deserve the most protection. A law firm's client files warrant stronger security than its lunch menu. Manufacturing companies prioritize protecting industrial control systems over employee break room schedules. These assessments guide budget allocation and implementation priorities.
Penetration testing simulates real attacks to identify weaknesses before malicious actors exploit them. Ethical hackers attempt to breach defenses using the same techniques as criminals, providing organizations with detailed reports about vulnerabilities and recommendations for remediation.
How Cyber Security Works to Stop Attacks
Technical mechanisms form the operational core of cyber security functions, creating barriers that attackers must overcome to reach their targets. Understanding these components clarifies how protection actually functions in practice.
Firewalls examine every packet of data attempting to enter or leave a network, comparing characteristics against security rules. A firewall might block all incoming connections to specific ports except from approved IP addresses, or prevent internal systems from communicating with known malicious domains. Configuration mistakes in firewall rules create security gaps—one misconfigured rule allowing unrestricted access can negate all other protections.
Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS) monitor network traffic for patterns matching known attack signatures. IDS alerts security teams to suspicious activity, while IPS actively blocks detected threats. These systems require constant updates as new attack patterns emerge—an IDS using outdated signatures might miss recently developed malware entirely.
Endpoint protection platforms secure individual devices against malware, ransomware, and exploitation attempts. Modern endpoint security goes beyond traditional antivirus by monitoring application behavior, blocking suspicious processes, and providing remote isolation capabilities. When an employee's laptop shows signs of compromise, security teams can immediately disconnect it from the network while investigating the incident.
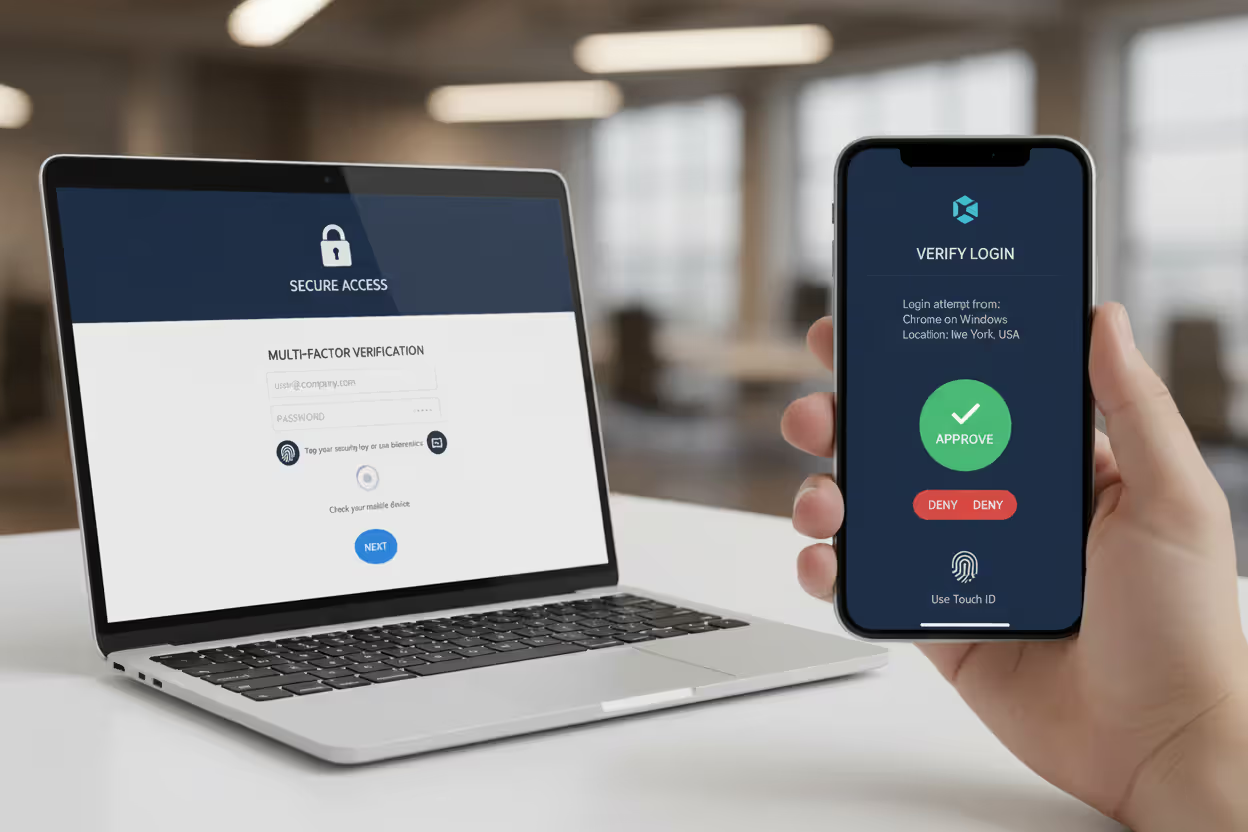
Authentication protocols verify that users are who they claim to be before granting access to systems. Multi-factor authentication (MFA) requires multiple verification methods—something you know (password), something you have (phone or security key), or something you are (fingerprint or facial recognition). MFA blocks most credential-based attacks, since stolen passwords alone can't provide access.
Author: Trevor Kingsland;
Source: elegantimagerytv.com
Security Information and Event Management (SIEM) platforms aggregate logs from across the infrastructure, correlating events to identify complex attacks that might appear benign when viewed in isolation. A single failed login attempt means little, but thousands of failed attempts across multiple accounts within minutes signals a credential-stuffing attack requiring immediate response.
Common Threats Cyber Security Defends Against
Understanding specific threats illustrates the purpose of cyber security and why comprehensive protection requires multiple defensive layers. Attackers constantly adapt their methods, exploiting new vulnerabilities and social engineering techniques.
Malware encompasses various malicious software types designed to damage systems, steal data, or provide unauthorized access. Trojans disguise themselves as legitimate programs while creating backdoors for attackers. Spyware monitors user activity and exfiltrates sensitive information. Worms self-replicate across networks, rapidly spreading infections. Each malware variant requires different detection and removal approaches.
Ransomware encrypts victim data and demands payment for decryption keys. Healthcare organizations face particularly severe impacts—encrypted patient records can force emergency departments to divert ambulances and cancel procedures. The average ransomware recovery cost exceeded $1.85 million in 2025, including ransom payments, system restoration, and business downtime. Many victims who pay ransoms never receive working decryption keys.

Author: Trevor Kingsland;
Source: elegantimagerytv.com
Phishing attacks manipulate victims into revealing credentials, downloading malware, or transferring funds to attacker-controlled accounts. Spear phishing targets specific individuals using personalized information that increases credibility. Business Email Compromise (BEC) scams impersonate executives to authorize fraudulent wire transfers. Employee training reduces phishing success rates, but sophisticated attacks fool even security-aware users.
Distributed Denial of Service (DDoS) attacks overwhelm systems with traffic, making websites and services unavailable to legitimate users. Attackers use botnets comprising thousands of compromised devices to generate massive traffic volumes. E-commerce sites lose revenue during downtime, while service providers face customer dissatisfaction and potential contract penalties.
Insider threats come from employees, contractors, or partners who abuse authorized access. Some insiders act maliciously, stealing data for personal gain or sabotaging systems out of grievance. Others cause breaches through negligence—leaving credentials on sticky notes, falling for phishing, or misconfiguring security settings. Insider threats prove particularly difficult to detect since the activity originates from legitimate accounts.
Zero-day exploits target vulnerabilities unknown to software vendors, giving defenders no time to patch before attacks begin. These exploits command high prices on underground markets, sometimes exceeding $1 million for critical vulnerabilities in widely used software. Organizations can't patch non-existent fixes, making defense dependent on behavior-based detection and network segmentation that limits exploitation impact.
When Organizations Need Cyber Security Measures
Every organization with digital assets requires cyber security, though implementation depth varies based on specific circumstances. Certain situations make robust security particularly urgent.
Compliance requirements mandate specific security controls for organizations handling regulated data. Healthcare providers must implement HIPAA security measures. Financial institutions face requirements from PCI DSS, GLBA, and various banking regulations. Government contractors must meet CMMC standards. Non-compliance results in fines, contract losses, and potential criminal liability for executives.
Data breach prevention motivates security investment after organizations recognize the costs of inadequate protection. Beyond immediate response expenses, breaches damage reputation, trigger customer churn, and invite regulatory scrutiny. Companies that experience breaches often face years of increased security spending while rebuilding stakeholder trust.
Business continuity planning incorporates cyber security responsibilities to ensure operations survive attacks and disasters. Ransomware can halt operations for weeks. DDoS attacks can make services unavailable during critical business periods. Supply chain compromises can disrupt manufacturing and logistics. Organizations with robust security and incident response plans recover faster and lose less revenue during incidents.
Customer trust increasingly depends on demonstrable security practices. Consumers choose service providers based partly on security reputation. Business customers require security certifications and audit reports before sharing sensitive data. Investors evaluate security posture when assessing risk. Strong security becomes a competitive differentiator rather than merely a cost center.
Mergers and acquisitions create security urgency as organizations integrate disparate systems and inherit the security debt of acquired companies. Due diligence processes now routinely include security assessments, with discovered vulnerabilities affecting deal valuations. Post-merger integration must address security gaps before they create breaches spanning the combined organization.
Frequently Asked Questions About Cyber Security
Cyber security serves as the essential foundation for modern digital operations, protecting organizations and individuals against constantly evolving threats. Its functions extend far beyond installing software—encompassing threat detection, incident response, vulnerability management, policy enforcement, and continuous monitoring across complex infrastructure.
The role of cyber security continues expanding as digital transformation accelerates and attack sophistication increases. Organizations that view security as strategic enablement rather than technical overhead build resilience against threats while maintaining customer trust and regulatory compliance. Those that neglect security face not whether breaches will occur, but when, and whether the organization survives the aftermath.
Effective protection requires understanding what cyber security actually does at technical, operational, and strategic levels. This knowledge enables informed decisions about security investments, appropriate implementation of controls, and realistic expectations about what security can achieve. No system becomes completely impenetrable, but comprehensive security makes successful attacks so difficult and costly that most attackers move to easier targets.
The cyber security responsibilities facing organizations will only intensify as technology evolves and threat actors develop new attack methods. Starting with fundamental protections—access controls, encryption, monitoring, employee training, and incident response planning—provides the foundation for more sophisticated security programs that adapt to emerging threats while supporting business objectives.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to cybersecurity awareness, online threats, phishing attacks, and data protection practices.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity risks and protection strategies may vary depending on individual behavior, technology usage, and threat environments.
This website does not provide professional cybersecurity, legal, or technical advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.