Cybersecurity analyst monitoring a large-scale cyberattack on digital infrastructure
Cyberattacks Explained
Content
Content
Remember 2000? The worst computer virus back then just displayed "I Love You" and scrambled some files. My college roommate lost his entire MP3 collection—absolutely tragic at the time. Fast forward to May 2021: Colonial Pipeline gets hit with ransomware and has to shut down. Suddenly, the Southeast can't get gas. People waited two hours to fill up. Prices jumped nearly a dollar per gallon overnight in Atlanta and Charlotte.
Equifax's breach in 2017? Their stock tanked 35% in two weeks. The CEO stepped down. Congressional hearings went on forever. All this happened because hackers exploited an Apache Struts vulnerability—one that had a patch sitting available for two full months before the breach.
What Are Cyberattacks?
Someone intentionally messes with your computers, networks, or data. Think of it like the difference between breaking into a building versus breaking into a database—same crime, different tools. The "intentional" part really matters. Laptop dies because you dumped coffee on it? That sucks, but it's not an attack. Someone secretly installs keylogger software to grab your banking passwords? Absolutely an attack.
What's in it for them? Money drives probably 90% of attacks. Cybercriminals want anything they can flip for cash: credit card numbers, login credentials, proprietary business stuff. Dark web marketplaces work exactly like eBay, except for stolen information. A complete identity package—full name, SSN, date of birth, address, mother's maiden name—goes for $50 to $200. Credit card details with CVV codes sell for $15 to $45 depending on the limit.
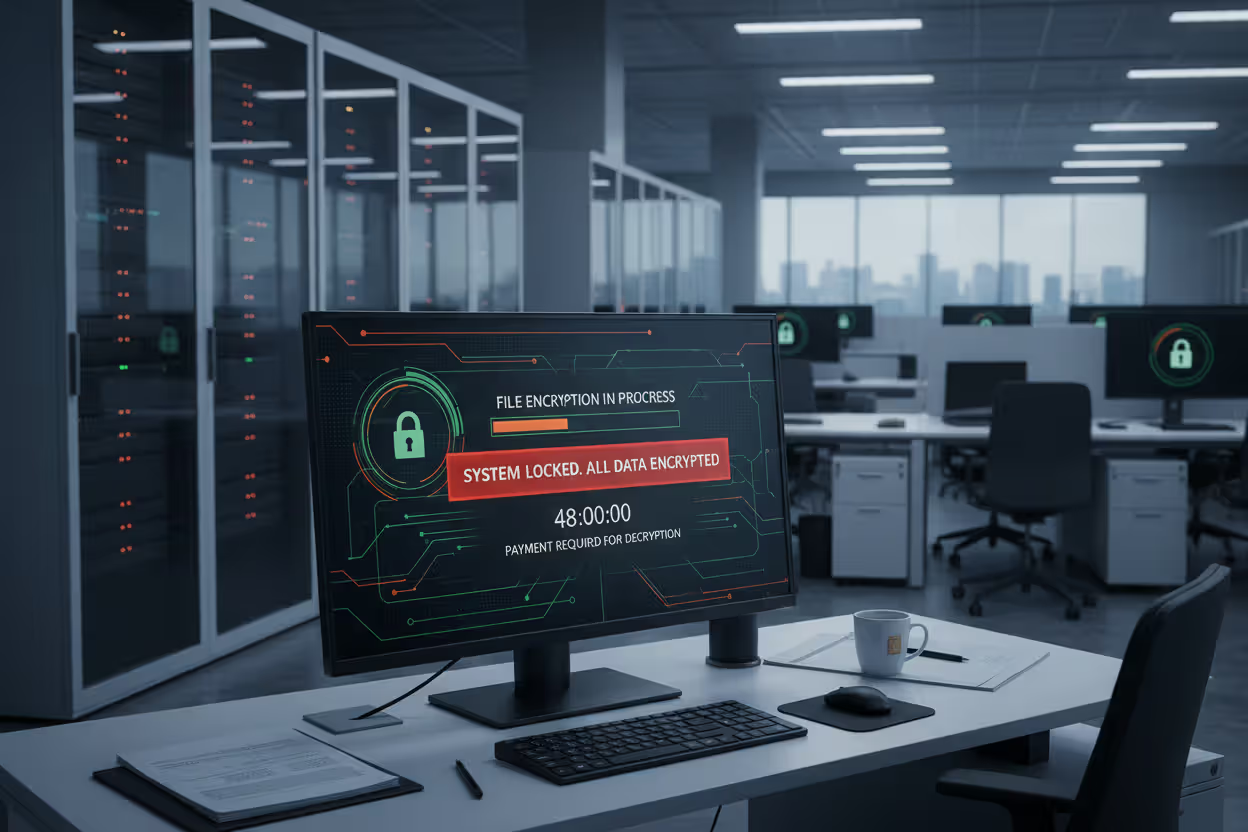
Ransomware works like a kidnapping. Bad guys encrypt every file on your systems, then demand payment—usually Bitcoin or Monero—to hand over the decryption key. Average ransom demands hit $2.5 million last year, up from $200,000 just three years back.
Politics motivates plenty of attacks too. Nation-states run espionage operations, stealing military tech, trade secrets, diplomatic communications. Why bother with physical spies when you can penetrate networks from another continent? Some attacks aim to sabotage instead of steal—disrupting elections, damaging critical infrastructure, creating general chaos.
Revenge drives insiders. Engineer gets fired after fifteen years, but his admin access doesn't get revoked fast enough. He deletes production databases before security catches up. Happens way more often than companies publicly admit.
Then you've got hackers chasing street cred in underground forums. They brag about breaches, post proof-of-concept exploits, compete for status.
Cybersecurity is much more than a matter of IT
— Stephane Nappo
Who launches these?
Cybercriminal organizations run like legitimate businesses, just illegal. They maintain development teams writing malware. Sales departments market stolen data. Some even run call centers providing "customer support" to ransomware victims struggling with Bitcoin payments. I'm serious—these operations have HR departments and performance reviews. Small and mid-sized businesses get hammered because they lack Fortune 500 security budgets but still handle valuable data.
State-sponsored teams get government funding and play the long game. APT28 (Russian military intelligence) spent years inside networks, slowly exfiltrating data to avoid detection. APT1, linked to China's People's Liberation Army, stole terabytes of intellectual property from 141 companies across 20 industries. These groups plan operations spanning months or years, carefully mapping networks before making moves.
Hacktivists chase ideological goals. Anonymous went after ISIS websites and social media accounts. Other groups leak corporate emails to expose alleged wrongdoing. They want publicity and political impact more than cash.
Insider threats already have legitimate access, which makes them particularly nasty. Sometimes it's intentional—employees selling customer databases to competitors. Other times it's accidental—someone falling for a phishing scam and handing over credentials. Verizon's 2024 Data Breach Investigations Report says insiders caused 20% of breaches.
These categories overlap constantly. Criminal groups take contracts from intelligence agencies. Hacktivists unknowingly advance nation-state objectives. The same malware serves multiple purposes depending on who's using it.
How Cyberattacks Work
Most attacks follow predictable patterns, though timelines vary wildly. Some ransomware operations go from initial breach to full encryption in under six hours. Nation-state espionage campaigns can unfold across years.
Attackers start by learning everything about you before making a move. They scan networks identifying what software versions you're running, which employees have admin privileges, whether your help desk actually verifies identities properly. They harvest employee names from LinkedIn. Purchase previously compromised passwords from earlier breaches—often available for pennies. Call your front desk pretending to be confused delivery drivers to gather building layout intel.
Next comes getting malicious tools to victims. A perfectly crafted email arrives looking exactly like legitimate FedEx notifications, except the tracking link downloads malware instead of showing package status. Compromised legitimate websites serve infected ads. In 2013, attackers scattered USB drives labeled "Executive Salary Information" across a company parking lot. Nineteen people plugged them in. All nineteen machines got compromised.
The payload activates when it hits a vulnerability. Maybe it leverages unpatched software your IT department kept postponing. Or a user clicked that fake FedEx link. Or cloud storage accidentally got configured to "public" access with default credentials still active. Zero-day exploits hit vulnerabilities vendors haven't discovered yet, so patches literally don't exist. Stuxnet used four different zero-days simultaneously—unprecedented at the time.
Maintaining access ensures attackers can get back in even after discovery. They create hidden admin accounts with innocent names like "SysUpdate" or "Backup_Service." Install backdoors that skip normal authentication. Modify system files so their malware loads automatically during startup. Some malware connects to command servers, sitting dormant until receiving instructions.
Expanding control happens next. Starting from one intern's laptop, attackers probe the network hunting for admin credentials and valuable databases. That intern's computer becomes a stepping stone. They climb from limited user privileges to domain admin rights, eventually controlling everything.
The endgame varies based on what attackers want. Ransomware operators encrypt everything valuable and post ransom demands. Corporate spies copy intellectual property to overseas servers—often throttling transfer speeds to dodge detection. Saboteurs delete or manipulate records. Some attackers just watch silently, documenting everything for future use.
What makes this possible? Predictable human and technical weaknesses. Software vulnerabilities that got patched six months ago but your systems haven't applied updates. Passwords like "Spring2024!" meeting complexity requirements while remaining totally guessable. Cloud configurations granting public internet access to internal databases. Remote access tools secured with single-factor authentication. And fundamentally, human nature—we click things we shouldn't, reuse passwords across twenty accounts, and trust authoritative-sounding voices over the phone.
Common Types of Cyberattacks
Let's look at specific tactics you'll actually run into.
Malware and Ransomware
Author: Calvin Roderick;
Source: elegantimagerytv.com
Malware covers any hostile software designed to damage, disrupt, or steal. Viruses need human action to spread—you open an infected document, triggering code that copies itself into other files. The 1999 Melissa virus spread through Microsoft Word documents, eventually infecting 250,000 computers and causing $80 million in damage.
Worms replicate automatically across networks without victims doing anything. The Morris Worm back in 1988 consumed so many resources that infected systems became unusable. Its creator meant it as a proof-of-concept but accidentally knocked 10% of the internet offline.
Trojans disguise themselves as legit software while performing nasty functions behind the scenes. That "free" PDF converter you downloaded? Might be logging your keystrokes. Spyware monitors everything—websites visited, passwords typed, files accessed—and transmits data to attackers.
Ransomware deserves special attention because it's catastrophically profitable. Modern operations like REvil and Conti run like actual corporations with specialized departments. These programs lock files using AES-256 encryption—effectively unbreakable without the key. Recent variants use "double extortion"—stealing sensitive data before encrypting it. Pay the ransom or we publish your customer database, financial records, and confidential communications publicly.
Attackers research targets thoroughly. Healthcare organizations get hit right before quarterly reporting deadlines. Law firms holding privileged communications face extortion threats. Manufacturers get attacked during peak production seasons when every hour of downtime costs hundreds of thousands. Average ransom payment reached $1.54 million in 2024, though demands often start at $5-10 million for large organizations.
Phishing and Social Engineering
Phishing uses fake communications—mostly emails—to manipulate recipients into harmful actions. Classic version: an email claiming your Netflix subscription failed, urging you to "update payment information" through a link leading to a fake login page that captures your credentials.
Personalized attacks zero in on specific individuals with tailored messages. In 2016, John Podesta, chairman of Hillary Clinton's presidential campaign, received phishing email disguised as a Google security alert. He clicked it. WikiLeaks published 50,000 stolen emails two months later.
The FBI reported that business email compromise scams cost companies $2.9 billion in 2023. Attackers impersonate executives, sending urgent instructions to finance departments requesting wire transfers for confidential acquisitions. Invoices arrive from email addresses differing by one character from legitimate vendors—accountsdepartment@acmevenḋor.com instead of accountsdepartment@acmevendor.com. See the difference? Neither did the victim who sent $500,000.
Social engineering manipulates psychology rather than exploiting technical holes. An attacker phones your IT help desk claiming to be a panicked executive locked out before a critical investor meeting. Creates enough urgency that support staff reset the password without proper verification. Someone follows employees through secure doors carrying coffee and boxes, looking hassled enough that stopping them feels rude.
These techniques weaponize normal human instincts—deference to authority, fear of consequences, desire to help, simple curiosity.
DDoS Attacks
Distributed Denial of Service attacks overwhelm systems with so much traffic that legit users can't access services. Imagine trying to enter Costco on Saturday, except there are 50,000 people blocking every entrance. Attackers control botnets—networks of compromised devices including security cameras, routers, DVRs, and smart refrigerators with default passwords still active.
The 2016 Dyn attack leveraged the Mirai botnet, comprising 100,000 infected IoT devices, to knock major websites offline including Twitter, Reddit, Netflix, and PayPal. Peak traffic exceeded 1.2 terabits per second—massive even by today's standards.
Application-layer attacks make excessive legitimate-looking requests that exhaust server resources. Protocol attacks exploit how TCP/IP handles connections, tying up infrastructure with incomplete handshakes. Volumetric attacks simply flood bandwidth with meaningless data until nothing else fits through.
While DDoS attacks typically don't steal data directly, they cause substantial damage. E-commerce sites lose revenue every minute they're unreachable—Amazon loses approximately $220,000 per minute of downtime. Cloud service providers violate SLA commitments. Stock prices drop when major services go offline. Sometimes DDoS serves as distraction, keeping security teams occupied fighting floods while attackers quietly exfiltrate data elsewhere.
Man-in-the-Middle Attacks
Man-in-the-Middle attacks position adversaries between two parties who think they're communicating directly. Picture someone intercepting your mail, reading it, possibly altering it, then forwarding it so neither sender nor recipient realizes anything happened.
Public Wi-Fi at coffee shops, airports, and hotels presents prime opportunities. Attackers set up rogue access points with names like "Starbucks_Free_WiFi"—identical to legitimate networks except controlled by criminals who monitor all traffic passing through.

Author: Calvin Roderick;
Source: elegantimagerytv.com
Session hijacking steals authentication tokens generated after successful login. The attacker doesn't need your password—just copies your active session identifier and impersonates you. Websites think they're talking to you because the session token matches.
SSL stripping downgrades encrypted HTTPS connections to unencrypted HTTP without obvious indicators. Everything looks normal on your screen—same website design, expected functionality—while attackers record every password, credit card number, and private message you transmit.
DNS spoofing redirects domain name lookups to attacker-controlled servers. You type "bankofamerica.com" but get sent to a perfect replica hosted elsewhere. Even the URL bar shows the correct address in some attacks.
These attacks often remain completely invisible. The website appears genuine. Responses arrive as expected. Meanwhile, someone records or modifies everything you send.
SQL Injection and Zero-Day Exploits
SQL injection targets database-driven websites by inserting malicious commands into input fields. When applications fail to validate user input properly, attackers manipulate database queries. A username field might accept: admin' OR '1'='1 which tricks poorly coded login systems into granting access without valid credentials.
A search box could be exploited to execute: '; DROP TABLE customers; -- which deletes your entire customer database. In 2012, SQL injection against South Carolina's Department of Revenue exposed 3.6 million Social Security numbers and 387,000 credit card numbers.
Zero-day exploits leverage security flaws unknown to software vendors. The name reflects vendors having zero days' notice to develop fixes. Bug bounty programs pay up to $2 million for critical vulnerabilities. Underground markets trade them for even more.
In 2021, four zero-days targeting Microsoft Exchange Server got exploited by APT groups, compromising an estimated 30,000 organizations in the United States alone. Microsoft released emergency patches, but attackers had already established persistent access to thousands of networks.
APT groups chain multiple zero-days together: one exploit breaches the perimeter, another escalates privileges, a third maintains persistence. Defending against unknown vulnerabilities requires assuming breach has already occurred and implementing layered security controls that function even when specific defenses fail.
Real-World Cyberattack Examples
Looking at major incidents reveals patterns that inform better defenses.
WannaCry (2017) infected over 300,000 computers across 150 countries within four days. This ransomware exploited EternalBlue, a Windows vulnerability leaked from NSA tools. Britain's National Health Service cancelled 19,000 appointments. Nissan halted production at UK plants. FedEx, Deutsche Bahn, Telefónica—all disrupted simultaneously.
Here's the maddening part: Microsoft released a security patch two months before WannaCry launched. Organizations that postponed routine updates paid dearly. A 22-year-old security researcher accidentally stopped WannaCry's spread by registering an unregistered domain hardcoded into the malware—essentially activating its kill switch. Estimated global damages exceeded $4 billion.
SolarWinds (2020) showed how supply chain attacks can slip past traditional defenses. Russian state-sponsored attackers inserted malicious code into Orion, network management software used by 18,000 customers including the Pentagon, Department of Homeland Security, Treasury Department, and Fortune 500 companies. When customers installed digitally-signed trusted updates through normal procedures, they granted attackers access to their most sensitive systems.
This breach remained undetected for eight months while extensive espionage occurred. FireEye discovered the compromise after attackers stole their Red Team penetration testing tools. The lesson? Even trusted vendors can become attack vectors.
Target (2013) exposed 40 million credit card numbers and 70 million customer records. Hackers stole credentials from Fazio Mechanical Services, an HVAC contractor with remote network access for monitoring store temperatures and energy consumption. From there, attackers installed malware on point-of-sale terminals during peak holiday shopping.
Target's security tools actually detected the breach and alerted staff, but those warnings got ignored. Target paid $18.5 million settling claims with 47 states, another $202.5 million to banks and credit unions, and suffered immeasurable brand damage. The CEO and CIO both resigned. Third-party vendor access demands strict segmentation and continuous monitoring.
Colonial Pipeline (2021) shut down infrastructure supplying 45% of East Coast fuel. Gas stations throughout the Southeast completely ran out. Panic buying emptied stations that still had supply. Prices spiked $0.87 per gallon in Atlanta, $0.62 in Charlotte. Airlines rerouted flights to avoid affected airports.
Attackers got in through a compromised VPN password—a legacy account without multi-factor authentication protecting it. Colonial paid $4.4 million in Bitcoin ransom, though FBI recovered approximately $2.3 million by tracing blockchain transactions. This incident accelerated federal regulations requiring critical infrastructure operators to report cyber incidents within 72 hours.

Author: Calvin Roderick;
Source: elegantimagerytv.com
Equifax (2017) exposed personal information for 147 million people—essentially half the US adult population—through an unpatched Apache Struts vulnerability. The breach persisted undetected for 76 days despite multiple compounding security failures.
The vulnerable server wasn't in their IT asset inventory. Automated vulnerability scans missed it. Manual inspections failed to identify it. SSL certificates had expired, breaking inspection tools. Network segmentation didn't prevent access to sensitive databases. Equifax faced over $1.4 billion in settlements, fines, and remediation costs. The CEO retired unexpectedly. This breach became required reading in cybersecurity programs—a textbook case of organizational dysfunction amplifying technical vulnerabilities.
How to Recognize a Cyberattack
Early detection dramatically reduces damage, yet many breaches persist for months. Verizon's 2024 report found median detection time of 207 days—nearly seven months of uncontrolled access.
Individual warning signs include:
Account activity you didn't authorize appears in your login history. Instagram shows someone accessed your account from Moldova at 3am Tuesday. Your bank statement lists ATM withdrawals in states you've never visited. Emails you definitely didn't write show up in your sent folder, often containing links trying to compromise your contacts.
Random password reset notifications flood your inbox—attackers trying to lock you out of your own accounts. Ransomware announces itself immediately with full-screen demands, but most malware operates silently, avoiding detection while stealing data or monitoring activity.
Device behavior changes warrant investigation. Sudden performance degradation—tasks that took seconds now require minutes. Frequent crashes. Browser toolbars appearing overnight. Your homepage changed to unfamiliar search engines. Hard drive activity lights blinking constantly when you're not running programs. Antivirus alerts shouldn't get dismissed as false positives without investigation.
Friends tell you they received weird messages from your Facebook account—links to weight loss pills or cryptocurrency scams. Your email contacts report suspicious attachments you supposedly sent.
Financial anomalies require immediate action: unrecognized charges appearing on credit cards, legitimate cards getting declined despite available credit, credit report inquiries you didn't initiate, new accounts opened in your name.
Organizational indicators include:
Network traffic patterns that don't match normal business activity. Connections to servers in countries where you have no operations. Large data transfers at 3:17am Sunday morning. Database queries requesting entire tables instead of specific records might signal SQL injection attacks or insider theft in progress. In 2023, a bank detected fraud when monitoring systems flagged a database admin downloading customer records at 11pm Friday—something he'd never done in five years of employment.
Suspicious system changes: security tools get disabled mysteriously, new user accounts get created outside normal processes, administrator groups show unexpected modifications, scheduled tasks appear that nobody authorized. Missing log files or gaps in logging suggest someone's covering tracks. One financial services firm discovered their breach when forensics revealed someone had deleted two weeks of security logs—which shouldn't be possible without admin privileges.
Employee reports deserve serious investigation. Unusual emails supposedly from executives asking for urgent wire transfers. Password reset requests they didn't initiate. Sudden inability to access files or systems they regularly use. Attackers frequently target help desk staff with social engineering, so unusual support requests need extra verification.
Performance problems might indicate cryptocurrency mining malware consuming system resources, ongoing DDoS attacks, or massive data exfiltration saturating network bandwidth.
Challenge: distinguishing attacks from normal IT chaos. One indicator might be coincidence. Multiple signals appearing together demand immediate investigation.
How Organizations Defend Against Cyberattacks
Effective defense assumes every control might fail eventually, requiring multiple overlapping layers.
Technical controls provide foundational protection. Firewalls filter network traffic based on security rules, blocking unauthorized connection attempts. Next-generation firewalls inspect application-layer traffic, identifying attack patterns even in encrypted connections. Intrusion detection and prevention systems monitor for known attack signatures and suspicious behavioral patterns.
Encryption scrambles data so stolen information becomes useless—attackers get meaningless gibberish without decryption keys. But implementation matters enormously. The Marriott breach exposed 500 million guest records that should have been encrypted but weren't. Weak algorithms or careless key management creates false confidence while providing zero actual protection.
Modern endpoint protection moved beyond signature-based antivirus that only catches known malware. Behavioral analysis and machine learning identify suspicious activity patterns—programs creating hundreds of encrypted files might indicate ransomware, even if the malware strain is brand new. Endpoint Detection and Response (EDR) platforms provide detailed visibility into everything happening on devices and enable rapid investigation.
Access controls contain damage when credentials get compromised. Multi-factor authentication requires something you know (password), something you have (phone receiving codes or hardware security key), and sometimes something you are (fingerprint or facial recognition). Stolen passwords alone become worthless without the second factor.
Least privilege principles grant users minimum permissions required for their specific job functions. The marketing intern doesn't need access to payroll databases. Network segmentation isolates critical systems, preventing attackers from roaming freely after breaching the perimeter. Regular access reviews identify and remove permissions people no longer need—former employees, transferred staff, contractors whose projects ended.
Patch management closes known vulnerabilities before exploitation. Conceptually simple, practically complex—coordinate patches across thousands of systems, legacy equipment without vendor support anymore, and limited maintenance windows. Organizations prioritize based on risk. Patches for actively exploited vulnerabilities get deployed within 24 hours. Less critical updates follow normal schedules. WannaCry specifically exploited organizations with poor patch management—the vulnerability had been fixed, but patches weren't applied.
Employee training addresses the largest vulnerability: humans. Effective programs move beyond boring annual compliance videos everyone clicks through while checking email. Simulated phishing attacks provide practice recognizing scams. Monthly micro-training covering recent tactics keeps security top-of-mind. Security-conscious culture encourages reporting suspicious activity and doesn't punish people for nearly getting fooled—punishment discourages reporting, so breaches go undetected longer.
Incident response planning prepares organizations for inevitable successful attacks. Plans specify who does what, communication procedures, evidence preservation requirements, and recovery procedures. Regular tabletop exercises expose weaknesses before actual emergencies. Retainer agreements with forensic specialists, attorneys specializing in breach response, and PR firms enable immediate action when time matters most. Colonial Pipeline's response got criticized partly because they lacked adequate preparation.
Security audits and testing identify weaknesses before attackers do. Penetration testing simulates real attacks against systems and applications. Vulnerability scanning automates searches for known security flaws. Red team exercises test whether people and processes actually detect and respond appropriately to threats—not just whether technical controls exist on paper. Third-party audits provide independent validation without organizational blind spots.
Backup and recovery capabilities let you restore systems without paying ransoms. But backups must be isolated from production networks—ransomware operators specifically hunt down and destroy backups to force payment. Recovery testing by actually restoring systems from backups exposes problems before emergencies. Organizations discovered they couldn't actually restore from backup right when ransomware struck.
Advanced organizations use zero-trust strategies: verify every access attempt no matter where it comes from, assume attackers already got in somewhere, implement tight segmentation limiting how far breaches can spread, and deploy automated security tools that respond faster than human analysts can manage.
Comparison of Cyberattack Types
| Attack Type | How It Works | Primary Target | Severity Level | Prevention Method |
| Ransomware | Uses strong encryption to lock files and demands cryptocurrency payment for decryption keys | Organizations with critical operations, healthcare facilities, manufacturing, municipalities with tight IT budgets | High | Maintain air-gapped backups tested regularly, implement advanced email filtering with attachment sandboxing, deploy EDR on all endpoints, run comprehensive security training |
| Phishing | Uses fake communications impersonating trusted entities to manipulate recipients into revealing credentials or downloading malware | Employees at every organizational level and individual consumers | Medium to High | Configure email authentication (SPF, DKIM, DMARC), provide continuous training with simulated attacks, require MFA across all accounts |
| DDoS | Floods systems with massive traffic from distributed compromised devices, blocking legitimate access | Public-facing websites, online services, financial platforms, gaming services | Medium | Deploy cloud-based traffic filtering services, utilize content delivery networks with DDoS mitigation, maintain excess bandwidth capacity, implement rate limiting |
| Man-in-the-Middle | Secretly intercepts and potentially alters communications between parties who think they're connecting directly | Users on untrusted networks, unencrypted connections, poorly configured mobile apps | Medium | Enforce strong encryption (TLS 1.3, VPN), use certificate pinning for applications, avoid public networks for sensitive transactions |
| SQL Injection | Runs malicious database commands through web application input fields lacking proper validation | Web applications with database backends, particularly e-commerce and SaaS platforms | High | Use parameterized queries preventing command injection, validate and sanitize all input, deploy web application firewalls, conduct regular security code reviews |
| Zero-Day Exploits | Takes advantage of security flaws that vendors don't know exist, so patches aren't available yet | High-value targets including government agencies, critical infrastructure, corporations with valuable IP | Very High | Build defense-in-depth with multiple control layers, use behavioral monitoring detecting anomalous activity, implement aggressive network segmentation, apply immediate patching when fixes become available |
Frequently Asked Questions About Cyberattacks
Cyberattacks keep evolving in scale, sophistication, and impact. What started as pranks and proof-of-concept experiments transformed into existential threats for businesses and serious risks for individuals. Our expanding attack surface—more connected devices, increased cloud adoption, deeper digital dependency—provides attackers growing opportunities.
Protection starts with understanding attack mechanics, recognizing warning indicators early, and building layered defenses assuming any single control will eventually fail. Perfect security doesn't exist in practice. Firewalls get misconfigured during routine changes. Employees click suspicious links despite comprehensive training programs. Zero-day vulnerabilities emerge without warning, leaving temporary windows of exposure. Success means assuming compromise will eventually occur and preparing accordingly through isolated backups, practiced incident response procedures, and resilient system architectures that continue functioning despite partial compromise.
The threat landscape evolves in concerning directions. Artificial intelligence simultaneously enables stronger defensive capabilities and more convincing attacks—AI-generated phishing emails pass human scrutiny at much higher rates. Quantum computing developments may eventually break current encryption standards, requiring migration to quantum-resistant cryptography. Internet of Things devices multiply attack vectors exponentially—some home networks now contain 30+ connected devices, most with minimal security. Geopolitical tensions increasingly manifest through cyber operations rather than conventional military action.
Maintaining adequate security requires continuous effort, regular updates to both knowledge and technical defenses, and accepting that cybersecurity affects everyone—not merely IT departments. Treat it as fundamental business risk and personal responsibility demanding ongoing attention, not a problem solved once and forgotten. The organizations and individuals who survive future attacks will be those who prepared before crisis struck, not those scrambling during emergencies.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to cybersecurity awareness, online threats, phishing attacks, and data protection practices.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity risks and protection strategies may vary depending on individual behavior, technology usage, and threat environments.
This website does not provide professional cybersecurity, legal, or technical advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.