Collage: worried person holding a smartphone, surrounded by dark silhouettes of scammers, background features large number "12.5" with dollar sign, screen shows phishing email and broken card
How to Identify and Avoid Online Scams?
Content
Content
The FBI's Internet Crime Complaint Center reported something alarming in 2025: Americans handed over $12.5 billion to internet fraudsters. Think about that number for a second. We're not talking about a few unlucky people—millions of individuals got duped while buying concert tickets, responding to what seemed like their bank's email, or helping someone they'd been messaging for months.
Here's what actually happened: criminals weaponized normal human behavior. They knew you'd panic if your account might close overnight. They counted on you wanting that incredible deal. They studied how to sound exactly like companies you trust.
Want to avoid becoming part of next year's statistics? You'll need to recognize manipulation tactics, spot the red flags professionals look for, and build habits that make you a harder target. Let's get into it.
What Are Online Scams and How Do They Work
Think of online scams explained this way: someone uses the internet—whether that's email, bogus websites, social media DMs, or text messages—to trick you into sending money or handing over private details. The scary part? While a street criminal targets maybe a dozen people daily, these digital operations hit millions of inboxes before breakfast, costing almost nothing to execute.
Why do smart people fall for these schemes? Scammers have mastered emotional manipulation. They'll slam you with urgency: "Click within 30 minutes or lose your account forever!" They trigger fear: "Law enforcement has flagged suspicious activity in your name." Or they offer something irresistible: "Congratulations! You're getting a $5,000 reward." Your brain's alarm systems go off, rational analysis shuts down, and suddenly you're acting on instinct rather than logic.
Author: Monica Ellery;
Source: elegantimagerytv.com
Before they contact you, criminals already know plenty. Data breaches have exposed billions of records. Your social media posts reveal your employer, family members, favorite brands, and recent vacation. Public databases show your address and property details. When a scammer emails pretending to be your actual bank, references your real account type, and knows you just moved—that personalization makes the fake message feel authentic.
Here's their playbook: First contact seems legitimate and helpful. They build rapport or escalate panic depending on the scam type. Then comes the ask—wire money, share your password, click this link, buy gift cards. Once you comply, your funds vanish through cryptocurrency tumblers or overseas accounts that investigators can't touch. Your stolen credentials get sold to other criminals within hours.
Common Types of Online Scams You Should Know
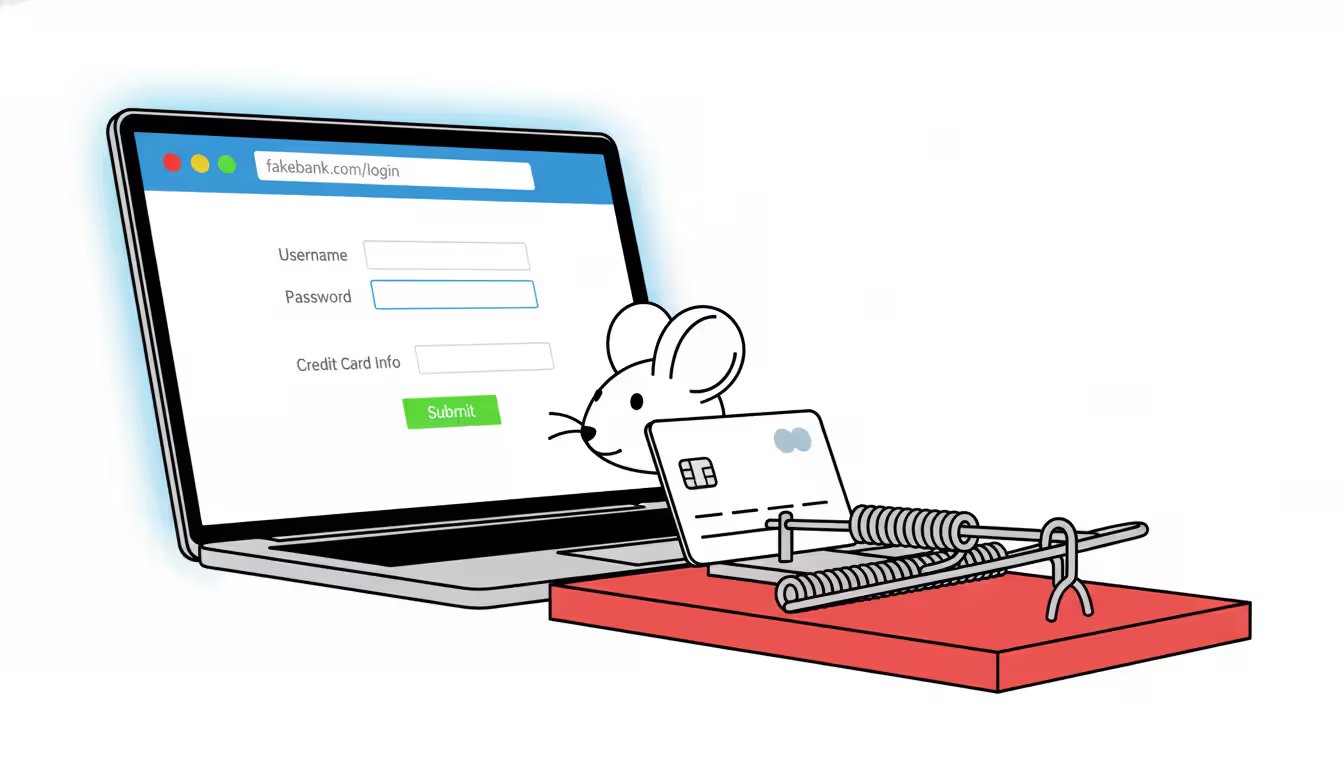
Phishing emails and copycat websites dominate the threat landscape. You'll receive messages claiming problems with your Netflix subscription, unusual Amazon purchases you didn't make, or compromised bank security. The email includes a convenient link to "verify your account"—except that website is a pixel-perfect forgery. Type in your username and password, and criminals now own your account. Sophisticated versions even bounce you to the legitimate site afterward, so nothing seems amiss.
Romance scams target people's deepest emotional needs. Fraudsters craft attractive dating profiles, invest months building genuine-seeming connections, then manufacture crises requiring financial rescue. Common stories include medical emergencies abroad, business deals gone wrong, or plane tickets to finally meet face-to-face (that meeting never materializes). Victims sometimes send money repeatedly, unable to accept they've been manipulated by someone who never cared.
Author: Monica Ellery;
Source: elegantimagerytv.com
Shopping fraud catches bargain hunters year-round but spikes during holidays. Sellers advertise brand-name products at 60-70% discounts, collect payment through methods that lack buyer protection, then vanish. Variations include shipping counterfeit knockoffs instead of authentic goods, bait-and-switch operations where you receive something completely different, or fake escrow services claiming to safeguard transactions while actually stealing your payment.
Investment and crypto scams promise wealth without risk—violating every principle of how markets actually function. Some operate as Ponzi schemes, paying early participants with newcomers' deposits to create an illusion of legitimacy. Others showcase fake trading dashboards displaying fantastic profits that don't exist. Try withdrawing your "earnings" and suddenly the platform has technical difficulties, additional fees appear, or you simply get blocked. Cryptocurrency transactions can't be reversed, making them especially attractive for fraud.
Tech support scams weaponize computer anxiety. Pop-up warnings announce viruses, hackers, or system failures, providing a phone number for "immediate assistance." Call that number and fake technicians pressure you into paying hundreds for unnecessary repairs, gain remote access to install actual malware, or steal passwords saved in your browser. Sometimes they even cold-call claiming to represent Microsoft or Apple, inventing problems with devices they couldn't possibly know you own.
Employment scams exploit people's financial desperation. Ads promote easy money working from home—but first you'll need to purchase training materials, equipment, or software. Check-cashing schemes ask you to deposit checks and forward portions via wire transfer; those checks bounce after several days, leaving you liable for the full amount. Reshipping operations make you an unwitting accomplice, forwarding stolen merchandise purchased with compromised credit cards.
| Scam Category | How They Hook You | What Should Make You Suspicious | Who Gets Targeted Most |
| Phishing | Urgent security alerts, delivery notifications, account verifications | Generic greetings like "Dear customer," links with misspellings, sender addresses that don't match companies | Anyone with email—especially busy professionals who skim messages |
| Romance | Gorgeous profiles, fast emotional bonding, eventual sob stories | Won't video chat despite weeks of talking, always an emergency right when you're close, sudden requests for Western Union transfers | People over 40, recently divorced, widowed, or lonely |
| Shopping Fraud | Unbeatable prices, "exclusive" limited offers, brand names for pennies | Brand new seller with zero feedback, won't use platform's payment protection, website created last week | Bargain shoppers, teenagers, holiday gift buyers |
| Investment | Guaranteed returns nobody else offers, celebrity endorsements, "insider" opportunities | Pressure to decide immediately, unregistered advisors, fees buried in confusing documents | Retirees with savings, inexperienced investors chasing quick wealth |
| Tech Support | Scary pop-ups claiming infections, robocalls about your computer | Pop-ups containing phone numbers (real warnings never do this), requests for remote desktop access, demands for iTunes cards | Seniors, people with limited tech knowledge |
| Employment | Work-from-home flexibility, be your own boss, earn thousands weekly | Asking you to pay them first, vague descriptions of actual work, unsolicited job offers when you weren't looking | Job seekers, college students, stay-at-home parents needing income |
Warning Signs That You're Dealing With a Scam
When someone pushes you to act right now—this minute, this hour, today—alarm bells should deafen you. Real businesses don't threaten to close your account in two hours. Actual opportunities don't evaporate if you sleep on the decision. Scammers manufacture artificial deadlines because they've learned something critical: reflection kills compliance. Give yourself time to think, and their manipulation loses power.
Payment method requests reveal intentions immediately. Someone wants you to wire money through Western Union? Send cryptocurrency? Purchase Google Play cards? That's not how legitimate transactions work, period. These payment types share one characteristic: they're permanent and untraceable. Your bank might use wire transfers for mortgage closings or major business deals, but they'll never demand you wire money to prevent account closure. Government agencies don't accept iTunes gift cards. That alone tells you everything.
Offers that violate basic economic reality should trigger skepticism automatically. Entry-level remote work paying $80 per hour? Designer handbags for 90% off retail? Investment strategies tripling your money in 30 days with zero risk? These scenarios ignore how markets, labor, and risk actually function. Genuine opportunities involve trade-offs. Scams promise unlimited upside with no downsides—because they're not real.
Communication quality often exposes foreign operations or careless criminals. While sophisticated scams maintain polish, watch for awkward phrasing that sounds slightly off, formatting inconsistencies within the same message, or email addresses that almost match legitimate domains. "security-team@paypa1-verify.com" isn't PayPal—that's a number one disguised as a lowercase L. Official corporate communications undergo quality control; fraudulent ones often don't.
Legitimate organizations never request sensitive information through email or unsolicited calls. Your credit card company already has your card number—why would they call asking for it? The Social Security Administration sends physical letters for official matters, not robocalls demanding your SSN. If someone contacts you out of nowhere requesting passwords, account numbers, or verification codes, that's a scam. Hang up and call the organization yourself using the number on their official website or your physical card.
Getting contacted about things you never initiated deserves automatic suspicion. You didn't enter their contest, so why are you a winner? You didn't submit a job application, so why are they offering you a position? Your computer manufacturer has no idea whether you're experiencing problems, so why would they call about viruses? Scammers make first contact because they're hunting. Legitimate businesses respond when you reach out to them.

Author: Monica Ellery;
Source: elegantimagerytv.com
Step-by-Step Guide to Verifying Suspicious Activity
Examining website legitimacy starts with scrutinizing the URL before entering any information. Secure sites display "https://" and show a padlock icon in your browser's address bar. Look specifically for spelling variations—"amazorn.com" or subdomains designed to deceive like "paypal-secure.verify-account.net" (the real domain there is verify-account.net, not PayPal). Try WHOIS lookup tools to check registration dates; supposed established retailers with websites created three days ago are obvious frauds.
Email sender verification requires looking past the friendly display name. An email labeled "Apple Security Team" might actually originate from "no-reply@apple-alert-dept.tk". Most email programs let you view full header information showing the actual source. Before clicking any links, hover your cursor over them—don't click yet—to preview the true destination URL in a small popup or your browser's status bar. Authentic companies maintain consistent domains across all correspondence.
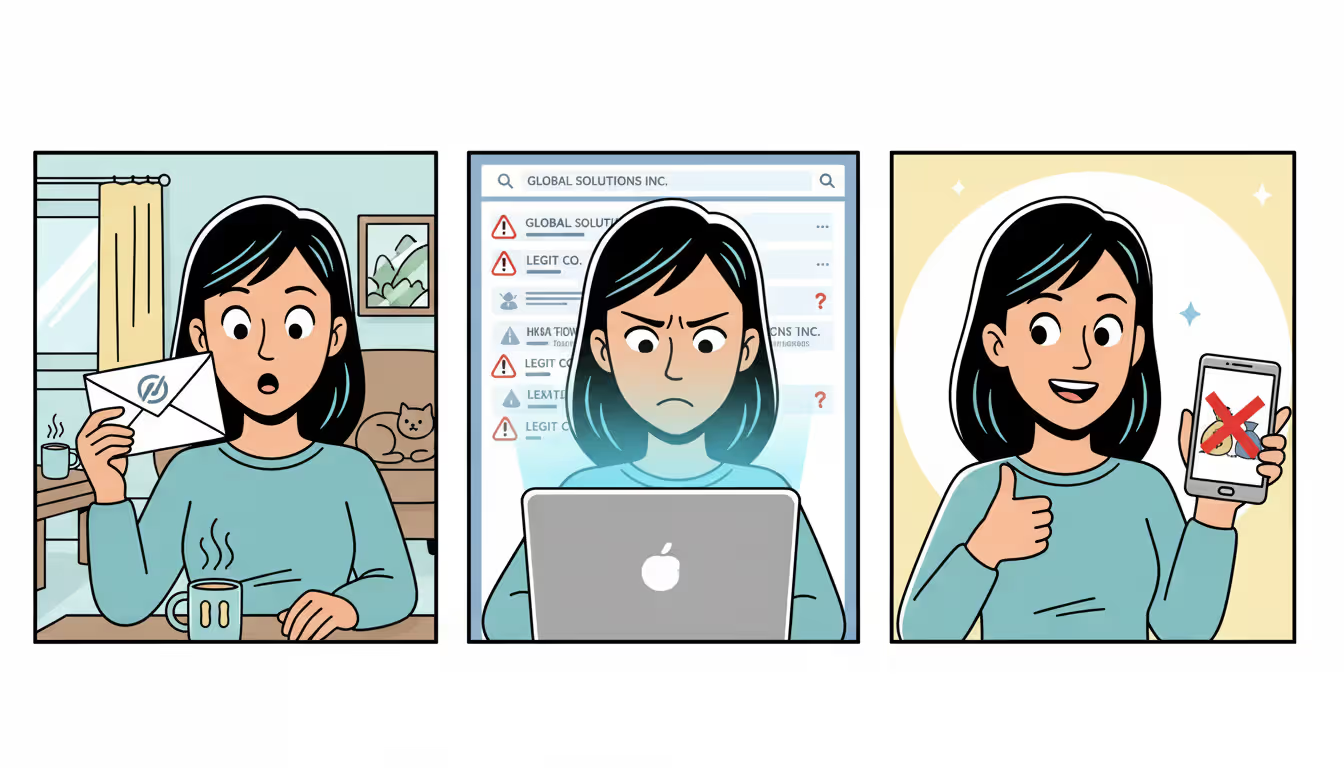
Researching companies takes five minutes and could save thousands. Search the business name plus words like "scam," "fraud," or "complaint." Previous victims usually share warnings online. Check Better Business Bureau ratings and complaint details. Verify business registration with your state's secretary of state office. For professional services, confirm licensing through state regulatory boards. If you're dealing with an individual, search their phone number, email address, and name independently—scammers frequently recycle fake identities across multiple schemes.
Reverse image searching catches stolen profile photos instantly. On most browsers, right-click profile pictures and select "Search image with Google" or use TinEye. That photo of your attractive online match appearing across 50 different dating profiles with different names? Stolen from a model's portfolio or stock photography. Real people's photos generally appear only on their own social accounts.
Scam databases and review aggregators provide crowdsourced intelligence. ScamAdviser analyzes website trustworthiness. Trustpilot and SiteJabber collect customer experiences. The FTC maintains Scam Alerts covering emerging threats. AARP's Fraud Watch Network tracks schemes targeting older adults. The Better Business Bureau's Scam Tracker maps reported fraud geographically. If a business or scheme has victimized others, someone has likely documented it.
Author: Monica Ellery;
Source: elegantimagerytv.com
What to Do If You've Been Scammed
Time becomes critical once you realize you've been defrauded. Contact your bank or credit union immediately if you sent money through wire transfer or provided bank account details—some institutions can recall or freeze transactions if notified within hours. For credit card charges, dispute them right away. Changed your password? Do it now across every account, prioritizing email and financial sites. If you installed software at a criminal's instruction, disconnect from the internet before that malware can do more damage, then run comprehensive antivirus scans.
Report what happened to create official records that support investigations and warn other potential victims. Submit details to the Federal Trade Commission through their ReportFraud.ftc.gov portal—they compile data that drives enforcement priorities. File a complaint with the FBI's Internet Crime Complaint Center (ic3.gov), especially if losses exceed $1,000 or the scheme involves multiple victims. Contact your state attorney general's consumer protection division, particularly when dealing with local businesses or service providers. Report phone-based scams to the Federal Communications Commission.
Notify your financial institutions within 24 hours of discovering fraud. Banks sometimes reverse transactions or recover funds when alerted quickly, though success rates vary dramatically by payment method. Credit card companies offer stronger consumer protections—federal law typically caps your liability at $50 for unauthorized charges if reported promptly, with many issuers waiving even that amount. Keep detailed records of every conversation, including representative names, reference numbers, and commitments made.
Document everything before evidence disappears. Screenshot fraudulent emails, text exchanges, and bogus websites—criminals often shut down domains within days. Save all communications chronologically. Retain payment receipts, transaction confirmations, and bank statements showing unauthorized activity. Write detailed timelines while events remain fresh in memory, noting dates, times, amounts, and what was said. This documentation proves essential for police reports, credit disputes, insurance claims, and potential civil litigation.
Monitor your credit reports aggressively after sharing Social Security numbers or other identity information. Pull reports from Equifax, Experian, and TransUnion through AnnualCreditReport.com without paying fees. Look for accounts you didn't open, inquiries you didn't authorize, or address changes you didn't request. Consider placing fraud alerts (free, renewable every year) or credit freezes (free, but you'll need to unfreeze when applying for legitimate credit) to block criminals from opening new accounts in your name.
Protecting Yourself From Future Scams
Author: Monica Ellery;
Source: elegantimagerytv.com
Defense starts with security software and browser safeguards. Apply operating system and application updates promptly—those patches fix security vulnerabilities criminals actively exploit. Install antivirus software from established companies that includes anti-phishing detection. Configure browsers to warn about suspicious sites. Ad-blocking extensions reduce exposure to malicious advertisements that sometimes appear even on legitimate websites. Password managers with security auditing identify weak or reused passwords across your accounts.
Password strength matters less than password uniqueness. Using the same password across multiple sites means one breach compromises everything. When attackers steal credentials from a random forum you joined years ago, they immediately test those credentials against banking sites, email providers, and shopping platforms. Every account needs its own distinct password. Yes, that's impossible to remember—that's why password managers exist. They generate complex random passwords and store them encrypted, requiring you to remember only one master password.
Two-factor authentication (2FA) protects accounts even when passwords leak. Enable it everywhere offered—email, banking, social media, shopping accounts. Authenticator apps like Google Authenticator, Authy, or Microsoft Authenticator generate time-based codes more secure than SMS text messages (which can be intercepted through SIM-swapping attacks). Hardware security keys like YubiKey offer maximum protection for high-value accounts, requiring physical possession to access accounts.
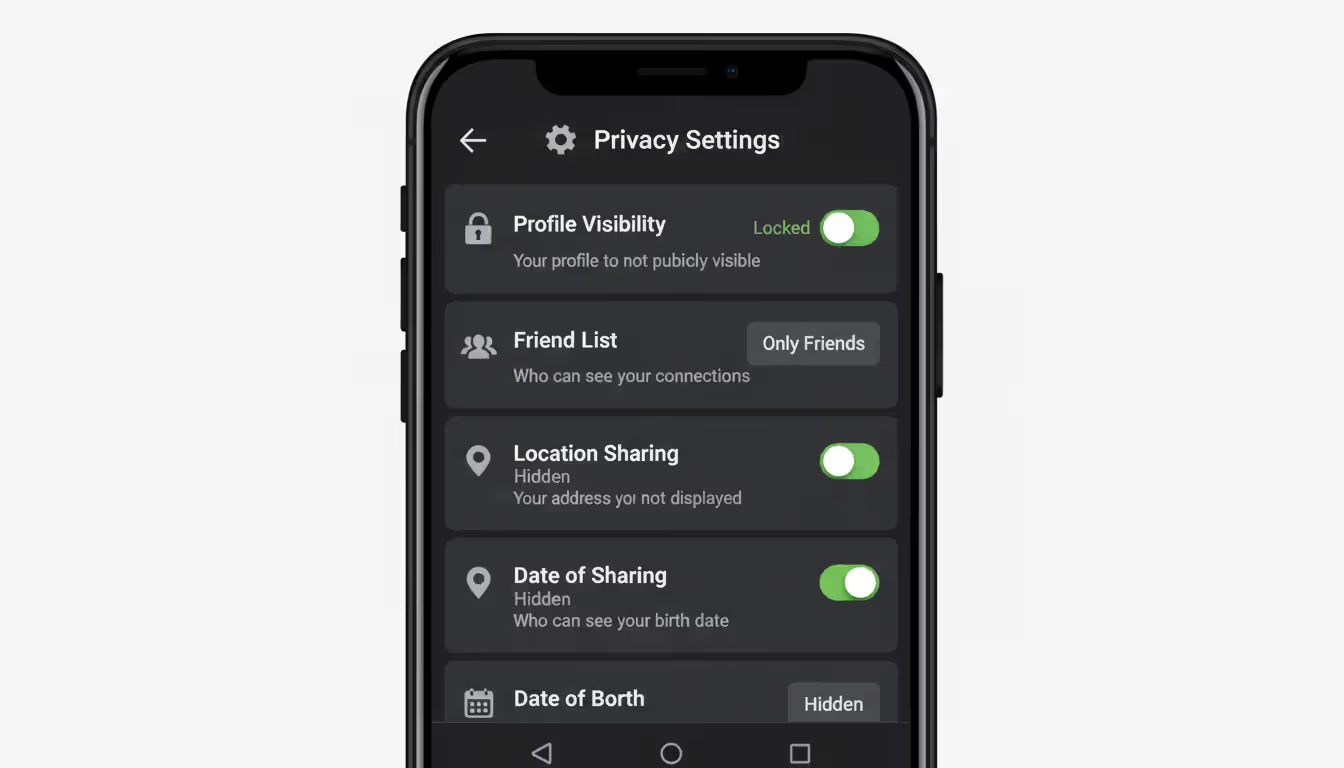
Tighten privacy controls on social media or criminals will mine your profiles for attack intelligence. Restrict profile visibility to confirmed friends rather than public access. Don't broadcast your location in real-time or announce when you'll be traveling (and your home empty). Avoid posting financial information, full birthdate details, or information that answers common security questions. Review and limit what others can tag you in. Each platform—Facebook, Instagram, LinkedIn, TikTok—has different default settings; adjust them individually rather than assuming privacy.
Education represents your best long-term defense because scam tactics constantly evolve. Fraudsters adapt as old schemes become recognized, creating new variations that exploit current events, emerging technologies, and new platforms. Follow consumer protection agencies on social media. Subscribe to alerts from the FTC and AARP's Fraud Watch Network. Discuss scams with family members, especially elderly relatives and young adults just gaining financial independence—both demographics face heightened risk from different scam categories. Healthy skepticism isn't cynicism; it's appropriate caution when threats are pervasive and sophisticated.
The sophistication of online fraud has increased dramatically. Criminals now use artificial intelligence to create deepfake videos and voice clones, making it nearly impossible to trust what you see and hear online. The best defense is a simple rule: verify everything through independent channels before taking any action involving money or personal information
— Kevin Mitnick
Frequently Asked Questions About Online Scams
Online scams work because they exploit fundamental aspects of human psychology—our tendency to trust, our emotional responses to fear and excitement, and our assumption that most people operate honestly. Criminals have industrialized deception, using technology to reach millions simultaneously while personalizing attacks with stolen data. The financial damage extends beyond immediate losses into damaged credit, compromised identities, and lasting psychological impacts that make victims question their judgment.
Your protection strategy needs to shift from assuming good faith to requiring verification. Before clicking any link, wiring any money, or sharing sensitive information, pause and independently confirm legitimacy through official channels. Leverage available verification tools—reverse image search, business registries, scam databases, and direct contact with organizations using phone numbers from their official websites, not ones provided by potential scammers.
Talk openly about scams with family and friends, especially those who may be more vulnerable. Criminals count on victims staying silent from embarrassment. Creating conversations around attempted fraud normalizes vigilance and builds community awareness that protects everyone.
Technology will continue evolving, bringing new scam variations we haven't imagined yet. But core protective principles remain constant: legitimate opportunities don't demand upfront payments, urgent pressure signals manipulation rather than opportunity, and offers that sound impossibly good almost certainly are. Listen to your instincts, verify independently, and remember that protecting yourself doesn't make you paranoid—it makes you informed.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to cybersecurity awareness, online threats, phishing attacks, and data protection practices.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity risks and protection strategies may vary depending on individual behavior, technology usage, and threat environments.
This website does not provide professional cybersecurity, legal, or technical advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.