
Phone receiver surrounded by digital cybercrime symbols on a dark background
Vishing Cyber Security Guide
Voice phishing—vishing for short—ranks among today's most successful cybercrime tactics. Email filters catch many scams before they reach your inbox, but a phone call? That rings straight through to your ear, demanding immediate attention while you're driving, working, or distracted. Scammers exploit something fundamental: we're hardwired to respond when someone addresses us directly.
Here's what should concern you: financial institutions logged voice fraud attempts climbing 350% between 2023 and now. American victims lost over $3.4 billion last year alone. The barrier to launching these attacks? Remarkably low. A prepaid phone, a basic script, and details scraped from Facebook or LinkedIn—that's all it takes for criminals to start calling.
What Is Vishing in Cyber Security?
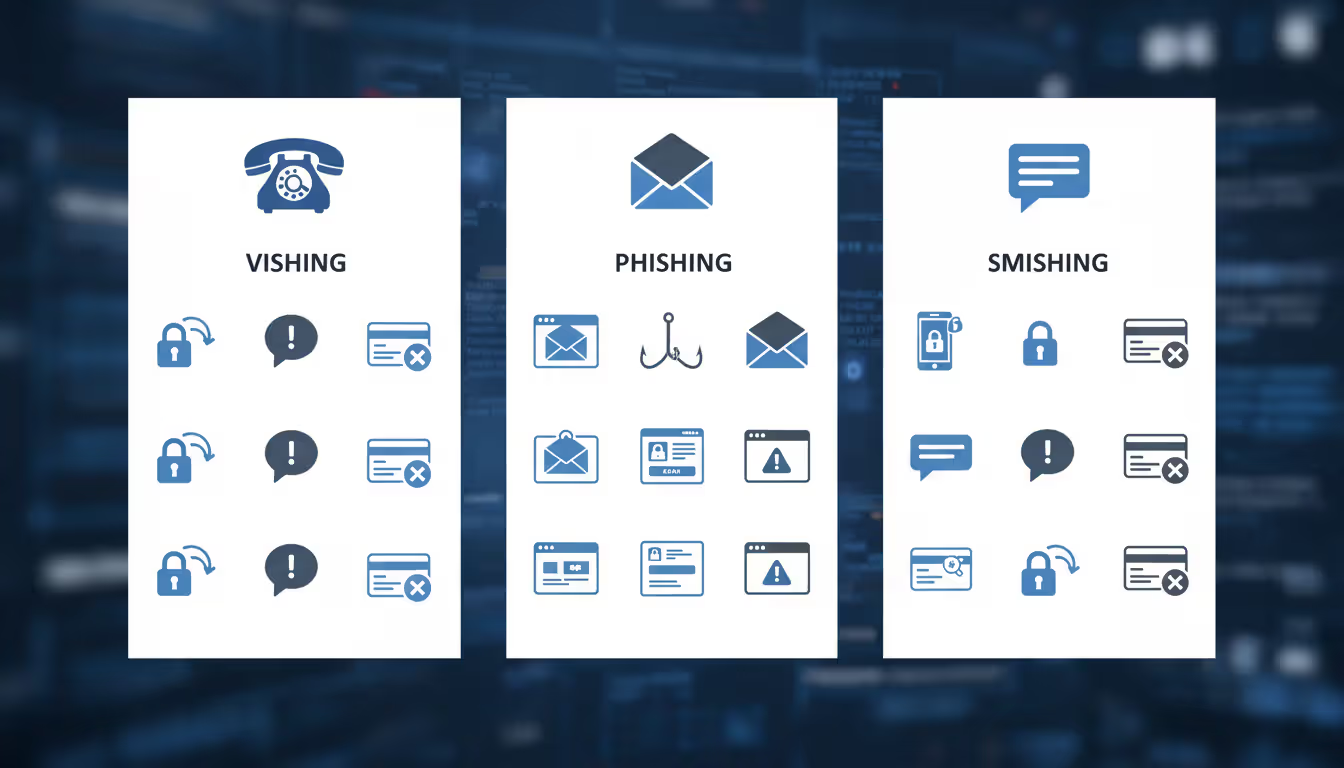
In cybersecurity terms, vishing describes fraud conducted through voice calls. Criminals phone targets directly, using psychological manipulation to extract sensitive data, trigger wire transfers, or gain system access. The word mashup of "voice" and "phishing" captures exactly what's happening—classic phishing cons delivered through your phone's speaker instead of your email inbox.
Traditional phishing arrives by email. Smishing comes through SMS texts. Vishing? That's your phone ringing with someone on the other end sounding official, concerned, or urgent. An employee who'd instantly delete a suspicious email might still comply when their "bank's fraud department" calls about unauthorized charges.
Why do attackers prefer calling? Phone conversations leave lighter digital traces than emails. No spam algorithm scans the conversation. No security system flags suspicious links. The real-time exchange prevents victims from pausing to research or consult colleagues. When someone tells you $4,800 just drained from your account, you're not simultaneously Googling "is this call legitimate?"

Author: Calvin Roderick;
Source: elegantimagerytv.com
Vishers deploy specific technical tricks: they spoof caller IDs to display trusted numbers, layer in call center background noise for authenticity, drop names of real employees they found on LinkedIn, and construct detailed cover stories explaining their "urgent need" for your information. Advanced operations now use AI voice synthesis to impersonate executives or family members—making verification through voice recognition essentially worthless.
The psychological engine driving vishing cyber security explained? Social engineering fundamentals: urgency (act now or lose money), authority (I'm from the government), fear (you're in trouble), and trust (we're here to help). Each scenario triggers emotional reactions that short-circuit rational decision-making.
How Vishing Attacks Work
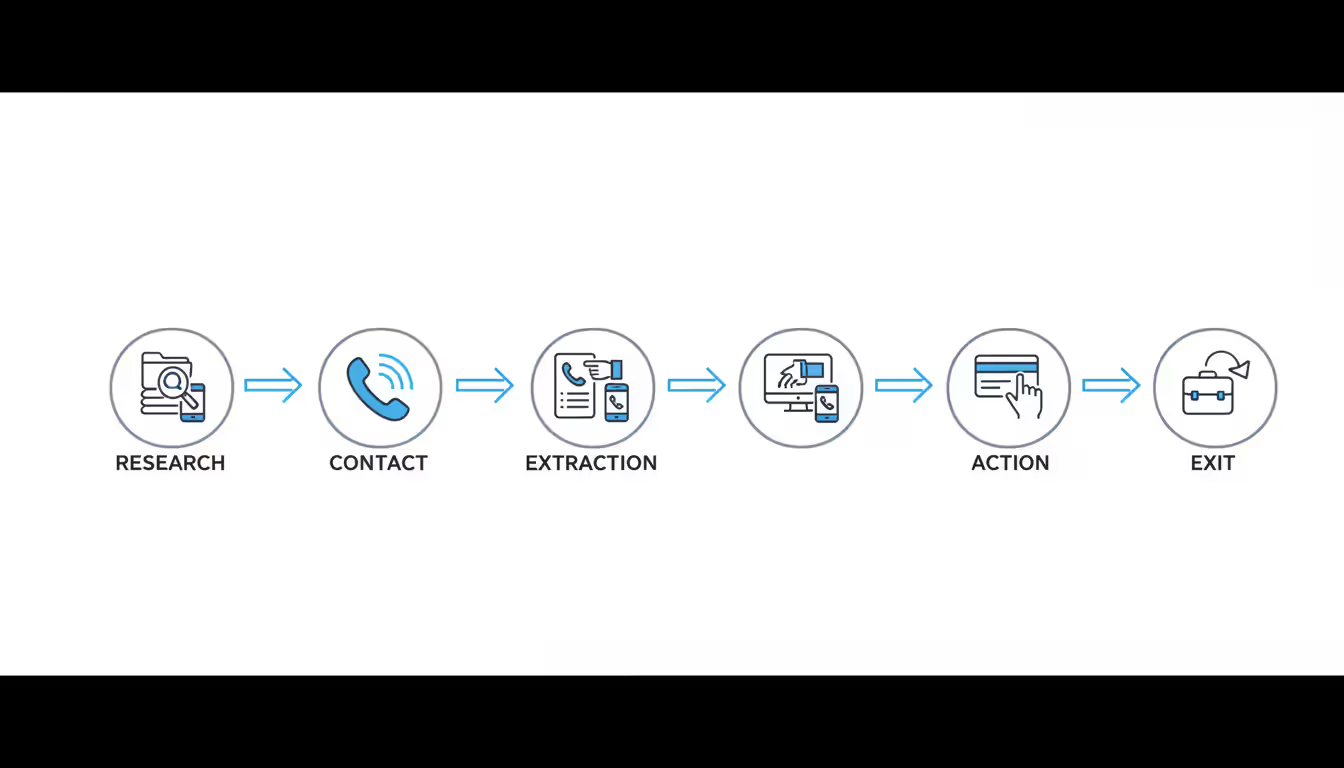
Vishing campaigns follow predictable patterns, though individual calls vary based on targets and goals.
Author: Calvin Roderick;
Source: elegantimagerytv.com
Research happens first. Before placing calls, attackers mine social media profiles, purchase data breach dumps, scan company websites, and search public records. They collect names, job titles, banking relationships, phone carriers, and personal details that make their stories believable. Targeting a small business owner? They'll know your bank's name, your payroll schedule, and possibly your accountant's name.
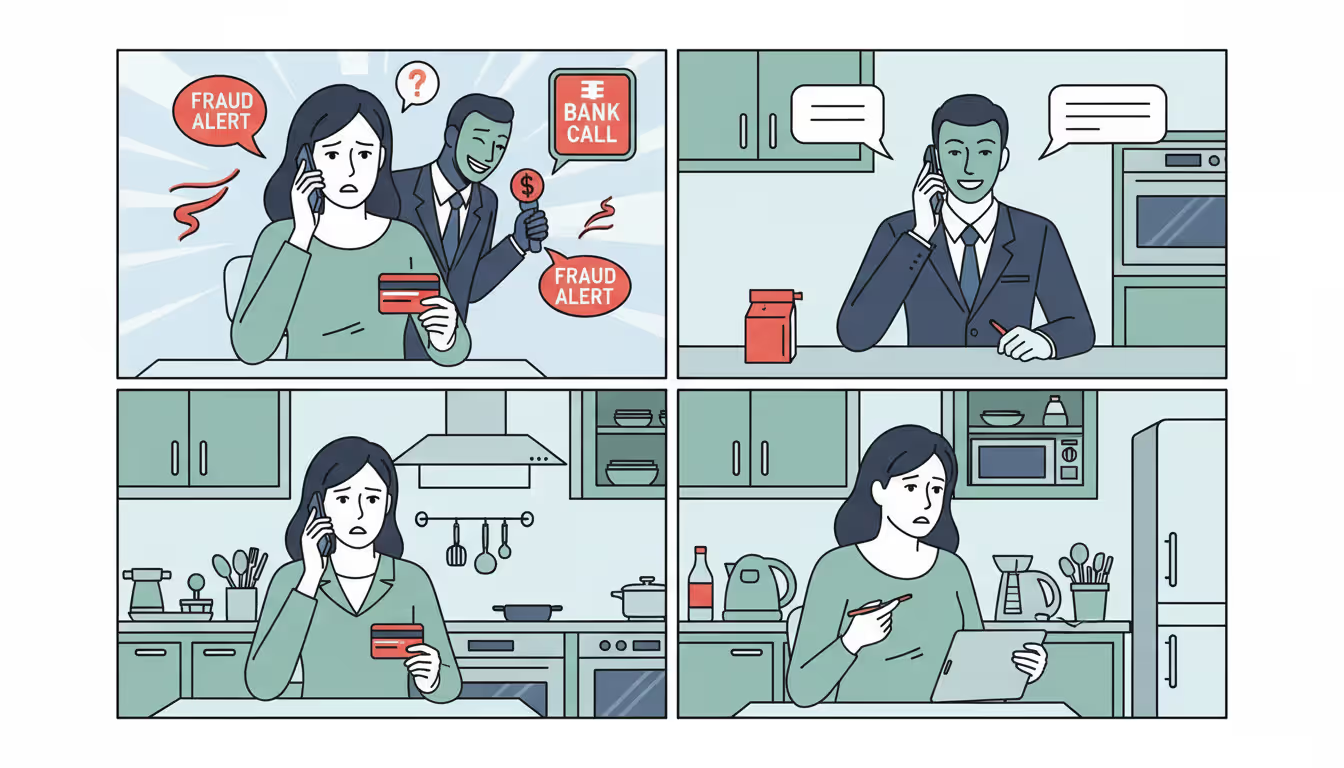
Contact establishes the scenario. The visher calls using a spoofed number matching the organization they're faking. They open with authority plus urgency: "First National Bank fraud prevention here. We just blocked three transactions totaling $4,800 on account 7392. I need to verify some details before we can release the holds."
Information extraction starts gently. The scammer requests "verification"—account numbers, Social Security digits, PINs, or those one-time codes your bank just texted. Each ask sounds reasonable individually, but combined they grant complete control.
The action phase applies maximum pressure. Now they want you to transfer funds to a "secure holding account," install "protective software" (actually remote access tools), or provide credentials to "prevent closure." Throughout this, they maintain urgency: delays mean financial loss or legal consequences.
Exit strategies cover tracks. After obtaining what they need, attackers claim everything's resolved, promise follow-up emails that never arrive, or simply disconnect. The goal: prevent immediate realization you've been scammed.
Psychological tactics include exploiting authority bias (posing as officials makes people compliant), creating artificial scarcity (limited time pressure), manufacturing social proof (others have been victimized), and weaponizing reciprocity (acting helpful while stealing information). Strategic silence proves particularly effective—pause after asking for sensitive data, making targets uncomfortable enough to fill the void by complying.
Spoofing technology costs shockingly little. Services under $20 monthly let anyone display arbitrary caller IDs. Some platforms supply background noise generators mimicking call centers, police stations, or bank offices. Voice modification apps alter age, gender, or accent presentations.
Author: Calvin Roderick;
Source: elegantimagerytv.com
Common Vishing Scenarios and Examples
Bank fraud calls dominate vishing cyber security examples. The caller claims they're from your bank's fraud team, references recent purchases (guessed or pulled from breached databases), and urgently demands your debit card details, CVV, and PIN to "block" fraudulent charges. Some vishers send targets to ATMs while staying on the line, walking them through "verification steps" that actually transfer money to criminal-controlled accounts.
Tech support scams target people less comfortable with technology. Callers claiming Microsoft, Apple, or ISP affiliation warn that viruses infected your computer or illegal activities occurred through your IP address. They guide victims to legitimate remote access software like TeamViewer, then install ransomware, harvest passwords, or lock machines demanding payment for "unlocking."
IRS impersonation intensifies during tax season but runs year-round. Scammers announce outstanding tax debts requiring immediate payment to avoid arrest. They spoof IRS phone numbers and use aggressive language—threatening wage garnishment, property liens, or deportation for immigrants. Reality check: the IRS always initiates contact through postal mail about unpaid taxes, never cold-calling with arrest threats.
COVID-related cons evolved throughout the pandemic and persist in 2026. Vishers impersonate health departments offering free testing appointments, vaccine scheduling, or stimulus payment verification. They collect Social Security numbers, bank details, and insurance information under "eligibility confirmation" pretexts.
Business email compromise with phone components adds vishing to traditional BEC attacks. After compromising executive email accounts, criminals call the finance department identifying as that executive. They reference the email (which accounting already received) and urgently request wire transfers for "confidential acquisitions" or "legal settlements." This two-channel approach—email confirmation plus voice verification—defeats many security checks.
Warning Signs of a Vishing Attack
Vishing cyber security warning signs cluster around urgency paired with information requests that legitimate organizations wouldn't make during unsolicited calls.
Urgency dominates nearly every vishing attempt. Listen for phrases like "your account closes in 30 minutes," "officers are dispatched to your location," or "final notice before legal action." Real organizations give reasonable timeframes and multiple contact opportunities.
Requests for sensitive information should trigger immediate skepticism. Your bank already has your account number—they don't need you to recite it. Government agencies verify identity through methods beyond Social Security numbers. Tech companies don't need remote computer access for problems they "detected"—you'd notice issues first.
Caller ID anomalies include numbers exactly matching the organization's public line (banks use separate outbound numbers), area codes mismatching claimed locations, or displays showing "Unknown" or "Restricted" when callers claim major institution representation.
Unsolicited problem reports deserve suspicion. Bank-detected fraud would trigger declined transactions you'd notice. Compromised computers show performance issues. Tax debts generate multiple postal notices before any phone contact.
Pressure preventing verification stops victims from independently confirming call legitimacy. Legitimate callers understand security concerns and encourage callback verification through publicly listed numbers.
Refusal to provide verification details—callback numbers, employee IDs, case references—signals fraud. Real organizations automatically provide these and expect callbacks through official channels.
Additional red flags: grammar errors or accent inconsistencies (though sophisticated vishers sound perfectly professional), artificial or inappropriate background sounds, unusual payment method demands (gift cards, cryptocurrency, wire transfers), and prize claims for contests you never entered.

Author: Calvin Roderick;
Source: elegantimagerytv.com
How to Identify and Verify Vishing Attempts
Learning how to identify vishing cyber security threats requires systematic verification protocols before sharing any information over the phone.
Verification starts with one rule: never provide sensitive data during unsolicited calls, regardless of apparent legitimacy. Someone claims they're from your bank, credit card issuer, or government agency? Tell them you'll call back using the number on your card, statement, or official website.
Checking caller legitimacy means ending the current conversation and independently looking up contact information. Don't use callback numbers the caller provides—those might route to accomplices. Don't redial the incoming number—spoofing can redirect callbacks to scammers. Instead, access contact details from sources you've found independently.
Questions revealing inconsistencies include requesting full names, employee IDs, departments, and direct callback numbers. Ask specific account questions only the real organization would answer—but never volunteer information yourself. Legitimate callers expect verification requests and won't act offended.
Official channel usage means checking your account through the banking app, logging into websites directly (never through emailed links), or visiting physical branches. Real issues appear through these official channels.
Recognizing AI-generated voices matters now that voice synthesis technology improved dramatically. In 2025, criminals successfully impersonated a CEO's voice to authorize a $2.3 million transfer. Watch for slight audio quality drops, unnatural speech rhythm, unusual background silence, or requests seeming out-of-character. Unexpected calls from executives, family members, or colleagues requesting urgent action? Verify through alternative communication methods before complying.
Business environments should establish verbal passwords or security questions for phone authentication. If your CFO calls requesting emergency wire transfers, finance teams need predetermined verification protocols—call back on known numbers and confirm through secondary channels like encrypted messaging.
How to Protect Yourself from Vishing
Learning how to avoid vishing cyber security attacks requires both personal vigilance and technical safeguards.
Never share sensitive data during unsolicited calls, period. This covers account numbers, Social Security digits, passwords, PINs, one-time authentication codes, credit card details—anything enabling identity theft or account access. Legitimate organizations already have this information or can verify identity through alternative methods.
Call-blocking tools available through carriers and third-party apps provide frontline defense. Major carriers now offer free or affordable services identifying potential spam, blocking known scam numbers, and verifying legitimate business calls. Apps like RoboKiller, Nomorobo, and Truecaller maintain crowdsourced databases of reported scam numbers with automatic blocking.
Two-factor authentication on all accounts—particularly financial and email—adds critical protection layers. Even if vishers obtain passwords, they can't access accounts protected by authentication apps or hardware keys. Skip SMS-based two-factor when possible—SIM swapping attacks intercept these codes.
Independent identity verification through official channels before taking action applies to banks, government agencies, tech support, and colleagues requesting unusual actions. Minutes spent verifying prevent significant losses.
Reporting suspicious calls helps authorities track campaigns and protect others. Contact the Federal Trade Commission through their fraud reporting website, submit complaints to the FBI's Internet Crime Complaint Center, and notify your phone carrier about suspected spoofing. These reports contribute to pattern recognition and enforcement actions.
Business employee training should include regular vishing simulations where security teams conduct practice attacks identifying vulnerabilities. Cover verification protocols, common scenarios, psychological manipulation tactics, and reporting procedures. Employees must know they won't face consequences for verifying unusual requests, even from apparent executives.
Additional protective steps: register on the National Do Not Call Registry (scammers ignore it but legitimate marketers comply), limit personal information shared online, monitor financial accounts regularly for unauthorized activity, and maintain healthy skepticism toward unsolicited calls claiming problems or opportunities.
High-value targets—executives, public figures—should consider using separate phone numbers for different purposes, limiting publicly available contact information, and implementing strict verification protocols for any requests involving financial transactions or sensitive information.
Author: Calvin Roderick;
Source: elegantimagerytv.com
What to Do If You've Been Targeted by Vishing
Quick action after falling victim to vishing limits damage and prevents additional losses.
Financial information shared? Contact your bank or credit card company immediately to freeze accounts, dispute unauthorized transactions, and request new cards. Most institutions run 24/7 fraud hotlines for these situations. Speed directly impacts recovery chances.
Social Security numbers or identity information provided? Place fraud alerts with all three major credit bureaus—Equifax, Experian, and TransUnion. These alerts force creditors to verify identity before opening new accounts in your name.
Software installed at a visher's direction? Disconnect the device from the internet immediately, run comprehensive antivirus scans, and consider professional forensics if the device contains sensitive business or personal data.
Reporting creates records potentially helping with financial recovery while contributing to law enforcement efforts. Submit reports to the FTC, FBI IC3, and local police departments. IRS impersonation cases should be reported to the Treasury Inspector General for Tax Administration.
Financial account monitoring should intensify after vishing incidents. Review bank statements, credit card activity, and credit reports weekly for several months. Unauthorized charges may appear gradually as criminals test stolen information.
Security freezes provide stronger protection than fraud alerts. Freezes prevent creditors from accessing your credit report, making new account openings nearly impossible for identity thieves. You can temporarily lift freezes when applying for legitimate credit.
Document everything about the incident for investigations and potential legal proceedings. Record dates, times, phone numbers (even if spoofed), caller claims, information you shared, and financial losses. Preserve related emails, texts, or screenshots showing communication.
Password changes for all accounts become critical, particularly if you shared passwords or security questions. Each account needs unique, strong passwords stored in reputable password managers.
Notify employers if vishing involved business information or occurred during work hours. Company security teams may need assessing whether broader system compromises occurred.
Identity theft insurance merits consideration if you face high future attack risk. These policies cover identity restoration expenses, legal fees, and lost wages from time spent resolving fraud.
Vishing represents the human element that technology alone cannot defend against.We've built sophisticated email filters and malware detection, but a phone call bypasses all of that. The attacker is speaking directly to the human brain, triggering emotional responses that override security training. Organizations that focus exclusively on technical controls while neglecting the social engineering component leave themselves fundamentally vulnerable. The most effective defense remains a culture where verification is expected, not optional, and where employees feel empowered to question unusual requests regardless of apparent authority
— Sarah Chen
Frequently Asked Questions About Vishing
Vishing cyber security threats keep evolving as criminals refine social engineering techniques and adopt technologies like AI voice synthesis. The core vulnerability stays constant: our tendency to trust voices, especially when they trigger emotions like fear, urgency, or respect for authority.
Protection demands skepticism toward unexpected calls, systematic verification before information sharing, and understanding that legitimate organizations accommodate security-conscious behavior. Your bank, the IRS, or tech support calls unexpectedly? The safest response never changes: disconnect and call back using contact information you've independently verified.
Minutes spent verifying call legitimacy represent minor inconvenience compared to months or years recovering from identity theft or financial fraud. As vishing attacks grow more sophisticated, your strongest defense stays simple: trust nothing, verify everything, and remember that urgency serves the scammer—patience protects you.
Related Stories

Read more
Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to cybersecurity awareness, online threats, phishing attacks, and data protection practices.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity risks and protection strategies may vary depending on individual behavior, technology usage, and threat environments.
This website does not provide professional cybersecurity, legal, or technical advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.




