
Abstract scene with data streams targeting a secure server and businessperson
Current Cybersecurity Threat Landscape Explained
Your organization's data sits in someone's crosshairs right now. Doesn't matter if you're a three-person startup or a Fortune 500 company. Today's cyber criminals have industrialized their operations, and nation-state hackers treat corporate networks like training grounds. The difference between staying secure and becoming tomorrow's breach notification? Understanding exactly what you're defending against and building defenses that actually work.
What Defines the Current Cybersecurity Threat Landscape
Think of the current cybersecurity threat landscape as every active digital danger pointed at your systems—malware campaigns, human hackers, automated bots, and everything in between. Here's what makes it tricky: these threats don't sit still. Last month's defense strategy might be useless today.
Your attack surface has blown up. Remember when securing a network meant defending a physical building's perimeter? Those days are gone. Sarah in accounting works from her kitchen table. Your customer database lives in AWS. That smart thermostat in the warehouse? It's running outdated firmware and connected to your main network. Each connection point gives attackers another door to try.
The professionalization of cybercrime changes everything. Criminal groups now operate like legitimate businesses, complete with customer service desks and money-back guarantees. Ransomware-as-a-Service platforms let script kiddies with minimal technical skills launch attacks that would've required expert knowledge five years ago. Dark web forums buzz with sellers hawking stolen credentials—someone's probably selling access to a system on your network right now for a few hundred dollars.
AI and automation have turbocharged both sides of this fight. Attackers deploy machine learning algorithms that write phishing emails mimicking your CEO's writing style—down to their habit of ending messages with "Thanks much" instead of "Thank you." Automated scanners probe millions of internet-facing systems daily, identifying vulnerable servers within hours of researchers publishing proof-of-concept exploits.

Author: Trevor Kingsland;
Source: elegantimagerytv.com
What drives these attackers? Money tops the list, but espionage, political activism, and pure chaos motivate different groups. A hospital might simultaneously defend against Russian ransomware gangs seeking Bitcoin payments while Chinese state-sponsored teams hunt COVID research data. Different motivations, different tactics, same compromised network.
Most Common Threats in Today's Cybersecurity Environment
Let's break down the attacks actually hitting organizations in 2026. You'll notice they don't look like Hollywood hacking scenes—no hooded figures typing frantically. Real attacks are methodical, patient, and devastatingly effective.
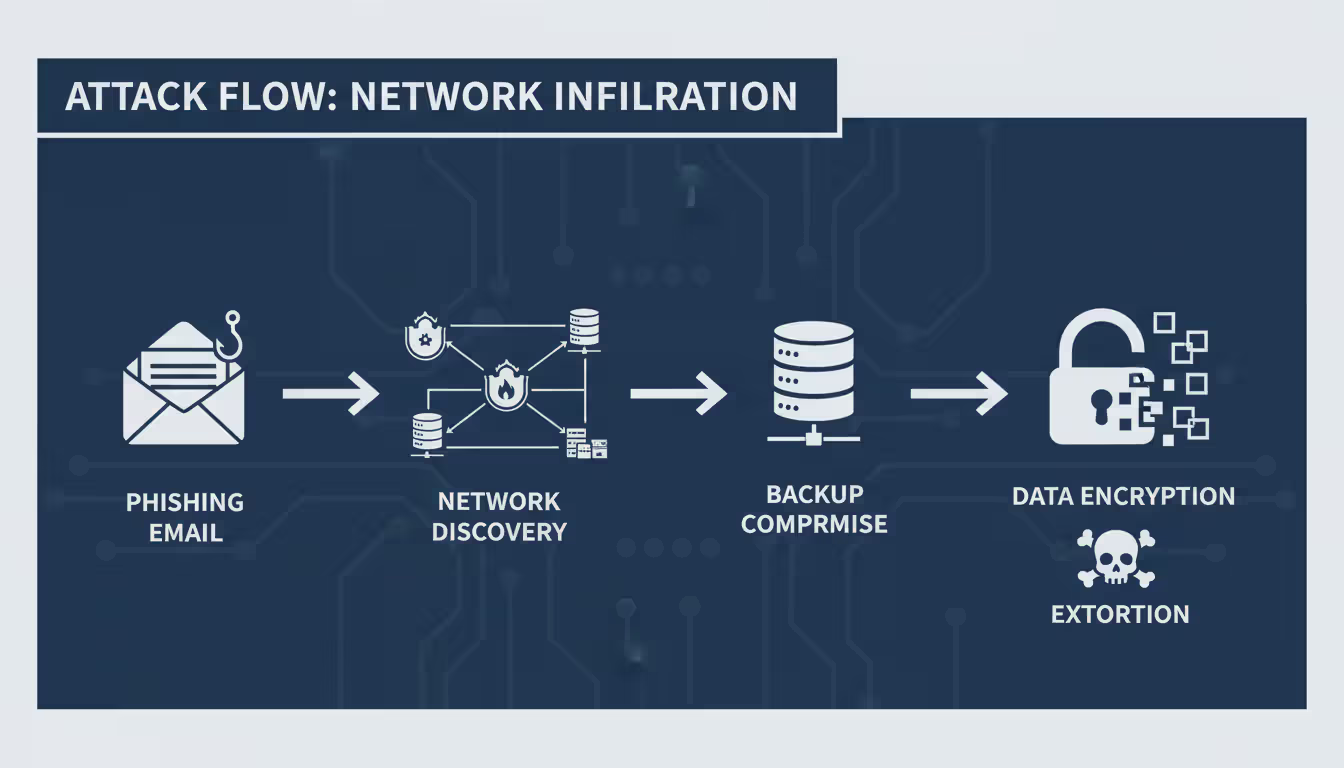
Ransomware and Extortion Attacks
Ransomware doesn't just encrypt your files anymore. Modern operators run sophisticated extortion schemes. They'll spend weeks inside your network, stealing proprietary data and customer information. Then comes the encryption. Then the demands: pay up or we publish everything. Some groups now contact your customers directly, telling them you got hacked and can't protect their data. Triple extortion adds DDoS attacks to the pressure campaign.
Here's how it actually unfolds: attackers gain initial access through a phishing email or compromised VPN credentials. Instead of immediately deploying ransomware, they go quiet. For 40-60 days, they map your entire network, locate your backups, and identify your most critical systems. They specifically hunt down and corrupt those backups—because they know you won't pay if you can restore everything. Only after thoroughly preparing do they flip the switch and encrypt everything simultaneously.
LockBit, ALPHV/BlackCat, and Cl0p dominated headlines through 2025. These groups run affiliate programs—the developers provide the malware, affiliates execute the attacks, and they split the ransom payments 70/30. Law enforcement takes down one operation, and three more pop up. It's cybercrime whack-a-mole.
Author: Trevor Kingsland;
Source: elegantimagerytv.com
Social Engineering and Phishing Schemes
Email remains the weakest link. Forget those obvious "Nigerian prince" scams. Today's phishing emails are researched, personalized, and convincing. Attackers scroll through your LinkedIn, find your recent projects, note who you work with, then craft emails referencing real initiatives and actual colleagues. Business email compromise schemes cost companies an average of $125,000 per successful attack.
Vishing and smishing complement email campaigns. Picture this: your CFO receives an email from the CEO's actual email address (compromised, not spoofed) requesting an urgent wire transfer for an acquisition. Thirty minutes later, someone calls claiming to be the legal department, confirming the transfer details. The coordination between channels makes it feel legitimate.
QR code phishing is the new headache. Security tools that scan URLs and email content can't read QR codes embedded in PDFs or images. Users scan the code with their phone, bypassing all the desktop security controls, and land on a credential harvesting page perfectly mimicking your Office 365 login.
Advanced Persistent Threats (APTs)
State-sponsored hacking teams play the long game. They're not after quick money—they want intellectual property, government secrets, or persistent access to critical infrastructure they can leverage during future conflicts. These groups will sit inside your network for years if you let them.
APTs stockpile zero-day vulnerabilities—security flaws that software vendors don't know exist and therefore can't patch. The 2025 MOVEit Transfer exploit demonstrated the damage: one zero-day, hundreds of compromised organizations, millions of stolen records. These vulnerabilities cost six or seven figures on the exploit market. Governments buy them. So do criminals.
Supply chain attacks let hackers compromise one vendor and inherit access to hundreds of downstream customers. Why break into 500 companies individually when you can hack the software they all use? The SolarWinds attack set the template. Now attackers target managed service providers, software update mechanisms, and third-party plugins as force multipliers.
Real-World Examples of Recent Cybersecurity Threats
Let me show you what this looks like when it hits.
February 2025: a hospital system serving 800,000 patients across six states got hit with ransomware. Emergency rooms went offline for three weeks. Ambulances diverted to facilities 40 miles away. Surgeries postponed. The attackers had infiltrated their network six months earlier through a phishing email targeting the HR department. They methodically identified and corrupted 47 backup repositories before deploying the encryption payload. Recovery costs exceeded $40 million. Two people died because of delayed emergency care.
A financial services company discovered in November 2025 that hackers had maintained database access for eighteen months. The breach happened through a third-party vendor's compromised credentials—a marketing analytics firm with overly broad database permissions. Attackers exfiltrated customer records slowly, just 50,000 records per week, staying below the threshold that would trigger data loss prevention alerts. Total compromise: 2.3 million customer records including Social Security numbers and account details.
Throughout 2025, renewable energy companies faced persistent attacks from state-sponsored groups hunting battery technology IP and smart grid management systems. Initial access came through spear-phishing emails with malicious attachments exploiting a PDF reader vulnerability. Once inside networks, attackers deployed custom malware disguised as legitimate Windows administration tools. Defense contractors and government labs weren't the only targets anymore—commercial clean energy companies found themselves in nation-state crosshairs.
A retail chain learned they'd been running point-of-sale malware across 300 stores for eight months. The malware captured payment card data during transactions, exfiltrating it through encrypted channels that appeared to be software update traffic. Entry point? An unsecured remote access tool used by HVAC contractors—identical to the Target breach attack vector from a decade earlier. Some lessons never stick.
How Modern Cybersecurity Threats Work
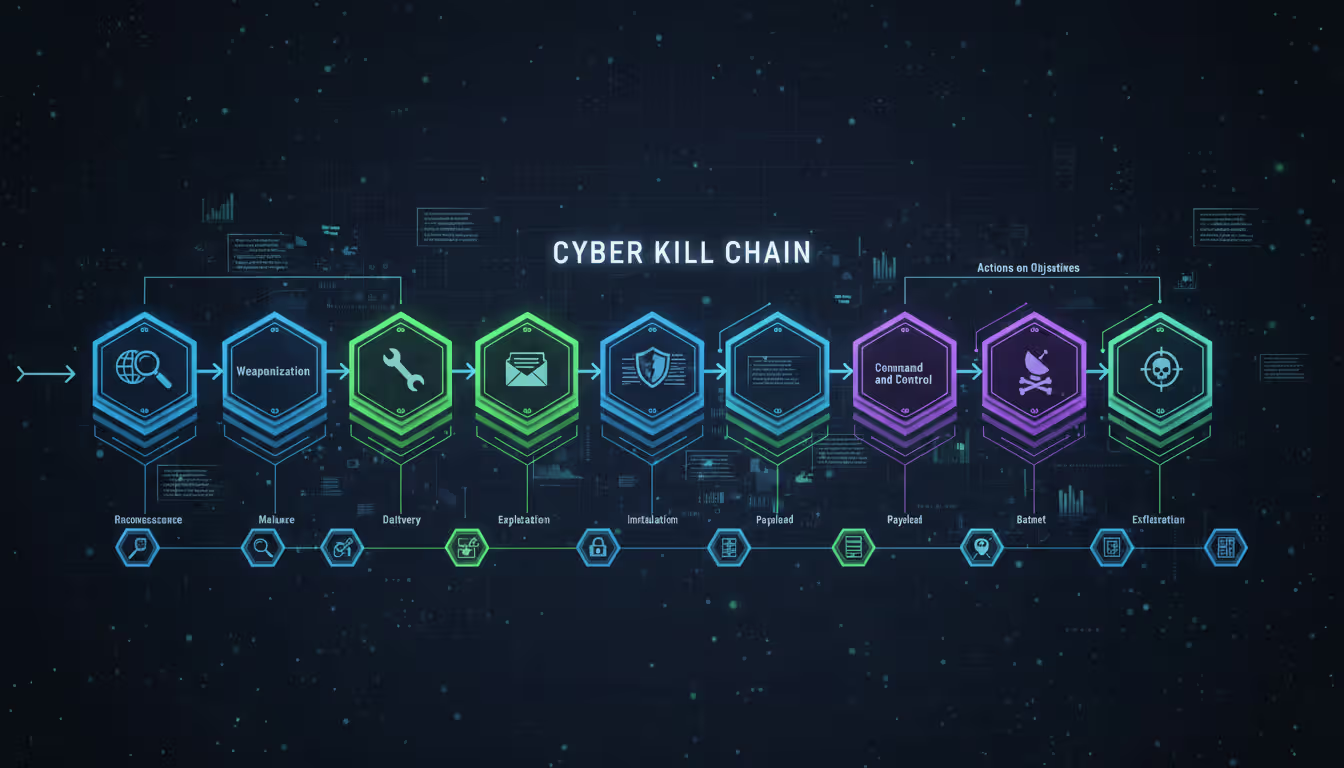
Understanding how these attacks unfold gives you fighting chances to stop them. The cyber kill chain breaks attacks into stages: reconnaissance, weaponization, delivery, exploitation, installation, command and control, then final objectives.
Reconnaissance means gathering intel. Attackers scan your public IP ranges looking for open ports. They browse your LinkedIn company page, noting what technologies your job postings mention. That listing for an Oracle DBA? You just told hackers exactly which database to target. They search breach databases for employee credentials from past compromises at other companies, betting your staff reused passwords.
Weaponization pairs exploits with payloads. Maybe they embed malware in a PDF that exploits a reader vulnerability. Perhaps they create a fake software update page mimicking your vendor's legitimate site. The weapon needs to bypass your security tools while delivering their actual attack code.
Delivery varies wildly. Email attachments still work shockingly well. Compromising websites your employees frequently visit (watering hole attacks) lets them deliver drive-by downloads. Some groups mail infected USB drives to physical offices, counting on curious employees to plug them in. Public-facing applications—VPNs, web servers, remote desktop—get hammered with exploit attempts constantly.
Exploitation triggers when victims open files, click links, or when automated exploits leverage unpatched vulnerabilities. That initial access might be a low-privilege user account, but it's a foothold.
Installation establishes persistence. Attackers create hidden administrator accounts, install remote access tools disguised as legitimate services, and modify system configurations to survive reboots. They typically install multiple backdoors—remove one, they've got three more.
Command and control establishes the callback connection to attacker infrastructure. Modern malware uses encrypted HTTPS connections that look like normal web browsing. Some malware queries legitimate services like Twitter or GitHub for commands, blending completely with normal traffic. Domain generation algorithms create thousands of potential callback addresses, making blocklists useless.
Actions on objectives depend on attacker goals. Ransomware operators encrypt files and post ransom notes. Espionage teams exfiltrate sensitive documents. Sabotage-focused attackers might corrupt databases, delete backups, or manipulate industrial control systems.
Lateral movement between systems lets attackers reach the crown jewels. They harvest cached credentials from memory, exploit trust relationships between servers, and escalate privileges through vulnerability exploitation or social engineering until they control domain administrator accounts—keys to the entire kingdom.
Author: Trevor Kingsland;
Source: elegantimagerytv.com
Warning Signs Your Organization May Be Under Threat
Attackers hide deliberately, but they can't be invisible. Watch for these red flags that suggest you're already compromised.
Unusual outbound traffic patterns deserve immediate investigation. Why is that accounting workstation connecting to servers in Romania at 3 AM? Legitimate business doesn't involve 40 GB uploads to cloud storage services your company doesn't use. Data exfiltration leaves fingerprints if you're watching.
Failed login attempts followed by success indicate credential stuffing or brute force attacks succeeding. Even weirder: successful logins from geographically impossible locations. Your VP authenticated from Chicago at 9 AM, then from Singapore at 9:15 AM? Someone's using stolen credentials.
New user accounts created outside business hours, especially ones with administrative privileges, scream "attacker persistence." Similarly, existing accounts suddenly getting permission upgrades or password changes you didn't authorize warrant immediate lockdown and investigation.
Unexpected software installations or mysterious running processes suggest malware deployment. Security tools disabled without IT authorization? You're almost certainly under active attack. Attackers kill EDR agents and antivirus before deploying ransomware.
Employees receiving unsolicited password reset emails or MFA push notifications signal someone trying to access their accounts. These social engineering attempts often precede successful account takeovers. One employee getting weird MFA prompts might be random—five employees reporting it means coordinated attack.
Files suddenly sporting extensions like .encrypted, .locked, or random character strings indicate ransomware encryption in progress. By the time users notice encrypted files, you've usually lost the race. Hours matter when ransomware deploys.
Database queries returning massive result sets or administrative tools running under regular user accounts suggest reconnaissance or data theft in progress. Baseline your normal operations so you recognize abnormal behavior.
How to Prevent and Mitigate Cybersecurity Threats
Preventing every attack is impossible. Determined attackers with time and resources will eventually find a way in. Your real goal? Detect them fast, limit their access, and prevent catastrophic damage. Layered defenses give you multiple chances to catch them.
Essential Security Controls for Organizations
Zero-trust architecture throws out the "trust but verify" approach. Instead, continuously verify everything. Users authenticate for each resource they access, not just once at network entry. That compromised laptop gets access only to resources that specific user legitimately needs—attackers can't easily pivot to other systems.
Multi-factor authentication stops most credential theft attacks cold. Stolen passwords become useless without the second authentication factor. But don't get complacent—attackers now use MFA fatigue attacks, flooding users with authentication prompts until someone approves one just to make them stop. Implement number-matching MFA where users must enter a displayed number rather than just approving a push notification.
Behavioral monitoring tools on workstations and servers spot suspicious activity that signature-based antivirus misses. Traditional antivirus knows malware X looks like this. Behavioral tools notice when Excel spawns PowerShell processes or when workstations start scanning internal networks—activities that might be legitimate but warrant investigation.
Network segmentation contains breaches. Separate your production environment from development systems. Isolate payment processing on dedicated networks. Put IoT devices on VLANs with strict firewall rules. Attackers who breach one segment shouldn't automatically access everything else.
Vulnerability management and patching prevent exploitation of known flaws. Focus on internet-facing systems first—those get hit constantly. Prioritize vulnerabilities that attackers actively exploit in the wild over theoretical risks. Risk-based approaches prevent wasting time patching internal systems for vulnerabilities that require local access while critical internet-exposed servers remain unpatched.
Backup protection requires equal attention to production systems. Store backups offline or use immutable storage that attackers can't encrypt or delete even with administrator access. Test restorations quarterly—untested backups fail when you desperately need them. One company discovered their backup tapes had been blank for two years. Testing would've caught that.
User training works, but only if done right. Annual compliance videos everyone clicks through accomplish nothing. Run simulated phishing campaigns with immediate teachable moments when people click—real-time feedback sticks. Make training relevant to actual threats your industry faces, not generic scenarios.
Individual User Protection Measures
The threat landscape has fundamentally shifted from opportunistic attacks to targeted operations with specific objectives. We're seeing attackers spend 40-60 days inside networks before deploying ransomware, using that time to identify and corrupt backups. The assumption that you can prevent all breaches is no longer realistic—organizations must build detection and response capabilities that assume compromise has already occurred
— Kevin Mandia
Personal security matters even if you're not technical. Configure automatic updates on all devices—operating systems, applications, everything. Most exploited vulnerabilities have available patches that victims never applied. Don't be that person running software three years out of date.
Use a password manager to create and remember unique passwords for every account. Reused passwords turn one breach into ten compromises. "But I can't remember 80 different passwords!" You're not supposed to—that's what password managers do. One strong master password protects your entire vault.
Question urgent requests demanding immediate action. Attackers weaponize urgency to bypass your critical thinking. Your CEO probably doesn't email you directly asking you to buy iTunes gift cards for a client emergency. Slow down, think, verify through independent channels.
Verify financial requests through separate communication methods. Email says wire $50,000 to vendor account? Call the requester using a phone number you looked up independently, not contact information from the suspicious email. Attackers compromise email accounts specifically to send these requests.
Avoid conducting sensitive activities on public Wi-Fi, or route everything through VPN services that encrypt your traffic. Attackers running rogue access points at airports and coffee shops intercept unencrypted communications, capturing credentials and session tokens that let them impersonate you.
Comparison of Major Threat Types
| Threat Type | Attack Method | Typical Targets | Average Damage Cost | Detection Difficulty | Prevention Complexity |
| Ransomware | File encryption combined with data theft and extortion demands | Healthcare organizations, local governments, educational institutions | $1.85M per successful attack | Medium—encryption activity creates detectable noise and user reports | High—demands multiple overlapping controls and tested recovery procedures |
| Phishing/BEC | Deceptive emails, text messages, or voice calls manipulating victims | Finance teams, C-suite executives, human resources staff | $125K per successful compromise | Low—employees frequently report suspicious messages when trained | Medium—requires ongoing user education plus email filtering technology |
| APT | Long-duration espionage using custom malware and stolen credentials | Government agencies, defense contractors, critical infrastructure operators | $4.5M+ per discovered incident | Very High—deliberately designed for stealth using legitimate tools | Very High—needs advanced threat hunting and continuous monitoring |
| DDoS | Overwhelming systems with massive traffic volumes from botnets | E-commerce platforms, online gaming services, banking websites | $220K per hour of service disruption | Low—immediately obvious when services become unavailable | Low—specialized mitigation services effectively counter most attacks |
Frequently Asked Questions About Cybersecurity Threats
The current cybersecurity threat landscape won't stabilize anytime soon. Threats that didn't exist two years ago now represent primary risks. Yesterday's cutting-edge defenses become today's baseline requirements. Organizations treating security as a compliance checkbox rather than operational imperative keep showing up in breach headlines.
Effective defense requires acknowledging uncomfortable realities. Determined attackers with sufficient resources, time, and motivation will eventually breach perimeter defenses. Accepting this doesn't mean giving up—it means shifting mindset from "prevent everything" to "detect quickly, limit damage, recover fast." This transformation separates organizations that survive sophisticated attacks from those that don't.
Budget allocation should reflect actual risk, not equal distribution. A company storing customer financial data needs different controls than one handling only publicly available information. Conduct realistic risk assessments identifying where security investments provide greatest protection. Spreading budgets equally across all systems dilutes resources and leaves critical assets underprotected while you're gold-plating low-risk systems.
Third-party risk management can't be ignored anymore. Your security is only as strong as the weakest vendor with network access or data custody. Contractual security requirements, regular third-party assessments, and network segmentation for vendor access reduce supply chain attack risks. Treating vendors as trusted insiders while they're running outdated systems practically invites compromise.
Incident response planning before crisis strikes enables faster, more effective responses when disaster hits. Tabletop exercises simulating ransomware attacks or data breaches identify gaps in procedures, communication, and decision-making authority. Who's authorized to take production offline? Who talks to media? Who negotiates with attackers? Answer these questions during practice, not during actual crisis. Organizations that rehearse incident response contain breaches 30% faster than those fumbling through first-time responses.
The threat landscape will keep evolving as attackers adopt emerging technologies and identify fresh vulnerabilities. Quantum computing threatens current encryption standards within the next decade. Deepfake technology already enables convincing video impersonation for social engineering. AI-powered malware that adapts to defenses in real-time is coming. Maintaining security requires ongoing investment in people, processes, and technology—not one-time projects but continuous improvement.
Organizations that understand current threats, implement layered defenses, and maintain vigilant monitoring can withstand attacks that will inevitably come. Perfect security doesn't exist—it's an impossible standard nobody achieves. Resilience that allows business operations to continue despite hostile action? That's achievable and worth every dollar invested.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to cybersecurity awareness, online threats, phishing attacks, and data protection practices.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity risks and protection strategies may vary depending on individual behavior, technology usage, and threat environments.
This website does not provide professional cybersecurity, legal, or technical advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.




